Globally, ransomware is big business, with millions of attacks targeting organizations every day. Not every attack is financially successful, but with keen attention to detail, attackers have (and continue to) tune tactics, making ransomware a...
Read More(Updated March 29th, 2024)
The National Vulnerability Database (NVD) has long been a crucial resource for organizations in managing their vulnerability lifecycle and ensuring the security of their systems. However, recent developments have...
Read MoreGartner® has published a new report focused onAutomated Moving Target Defense (AMTD) technology innovation. According to Gartner: “Combining AMTD solutions at different layers of the technology stack provides innovation leaders with a highly...
Read MoreThere’s now a new ransomware attack, on average, every 10 seconds. Threat actors have become powerful and sophisticated enough to successfully hold national governments—such as Ireland and Costa Rica—to ransom.
Read MoreFew executives doubt their organizations must pay more attention to cybersecurity. Cybercrime costs were estimated at $8.4 trillion globally in 2022 alone, and could exceed $20 trillion by 2026. No organization can afford to ignore this risk.
Read MoreFileless malware attacks are a malicious code execution technique that works completely within process memory. In a fileless attack, no files are dropped onto a hard drive. With no artifacts on the hard drive to detect, these attacks easily evade...
Read MoreMorphisec has recently identified a highly evasive malware campaign delivering ProxyShellMiner to Windows endpoints.
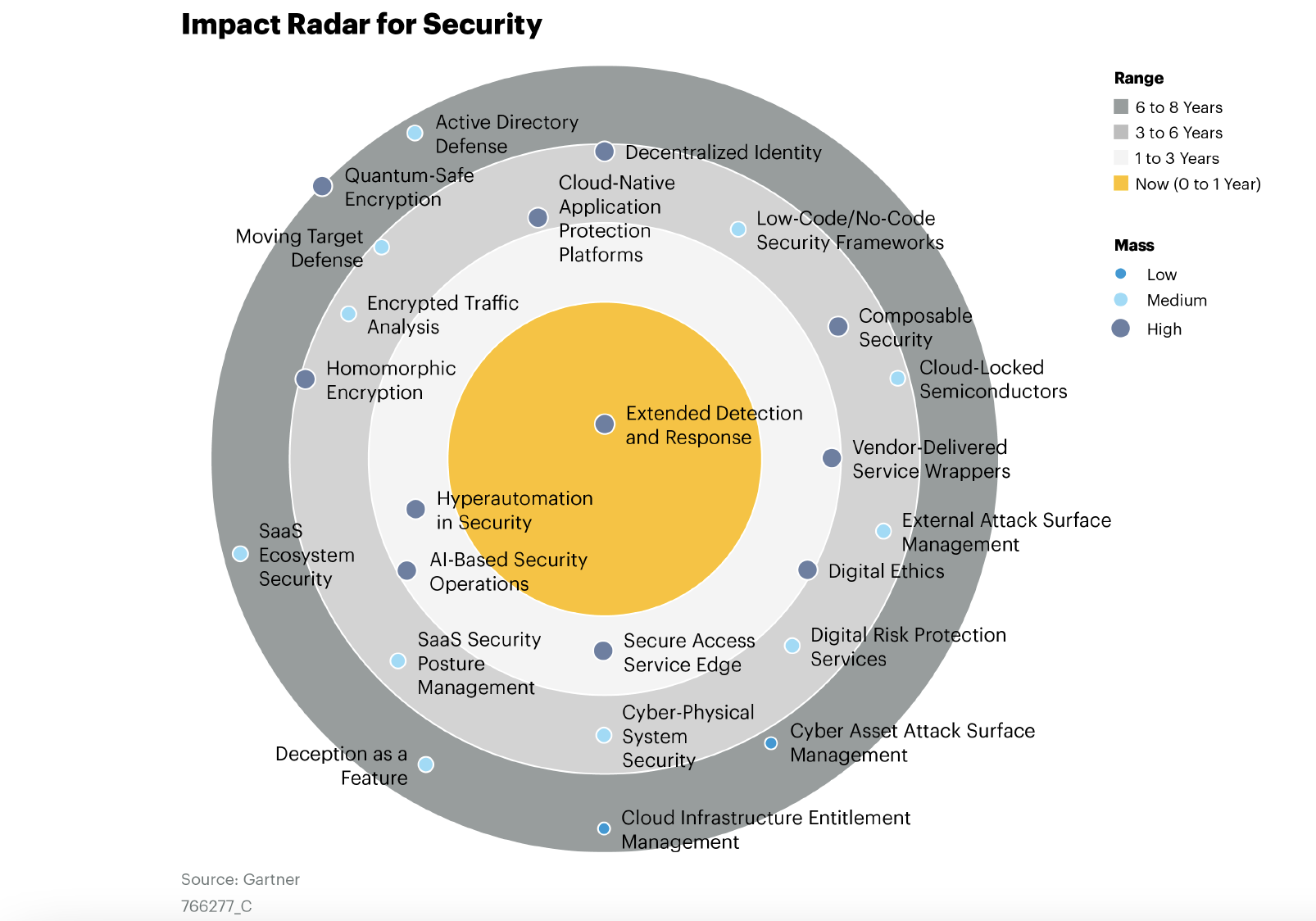
Read MoreFor the second consecutive year, Gartner has highlighted Moving Target Defense (MTD) as a featured technology, and Morphisec as a Sample Vendor for the technology in their report, Emerging Tech Impact Radar: Security. The authors define MTD as “......
Read MoreOn a scale of one to ten, how effective is the status quo approach to server security?In theory, it should be ten. The path to keeping servers protected from the outside world (segmentation, firewalls, vulnerability patching, security solutions...
Read MoreThe evidence is clear that despite expanding cybersecurity investment, sophisticated cyberthreats are increasingly successful. Household brands like Uber and Apple, essential service providers like Colonial Pipeline, and even entire nation states...
Read MoreIn the last couple of years, security teams in large enterprises and high-profile government organizations have increasingly experienced a new form of attack. This attack leverages the supply chain of an organization’s software ecosystem (and less...
Read MoreOn the dark web, private health information (PHI) sells for up to $1,000 per record. In response to surging healthcare cyberattacks, it's now glaringly obvious that data security in healthcare needs to go in a new direction.
Read MoreIn the last few years, organizations in every sector have witnessed a clear shift in the threat landscape. Although the number and frequency of all kinds of cyberattacks increased, ransomware in particular has undergone extremely rapid evolution....
Read MoreShoe shops and security operation centers have something in common. One size fits all solutions are not a great idea in either area. Unfortunately for security professionals trying to secure Linux servers, purpose-built Linux solutions are...
Read MoreNot long ago, the term “Linux protection” was closer to an oxymoron than a strategy. For security teams and vendors alike, Linux systems were seen as being either immune to cyber threats or not something threat actors targeted.
Read More"Make do and mend." If you work in IT security, this slogan, from a pamphlet issued by the British government in 1943, probably resonates. In security, constant mending—i.e. patching, is a fact of life. So what is virtual patching and why would you...
Read MoreRansomware attacks have never been more dangerous, or prolific. 2020 was described by security experts and media outlets as the "worst year ever for ransomware." Then ransomware attacks grew by 105 percent between 2020 and 2021. This cyberwar has...
Read MoreFor small and medium businesses (SMBs), digital transformation has been a double edged sword. Cloud technologies and IoT devices have boosted productivity during a punishing pandemic where every dollar counts. But these advances have come at a cost....
Read MoreSearch Our Site
Recent Posts
Posts by Tag
- Moving Target Defense (129)
- Cyber Security News (124)
- Morphisec Labs (113)
- Threat Research (64)
- Threat Post (61)
- Morphisec News (52)
- Automated Moving Target Defense (11)
- Defense-in-Depth (6)
- in-memory attacks (6)
- Gartner (4)
- Ransomware (4)
- runtime attacks (4)
- Legacy security (3)
- Linux cyber security (3)
- advanced threat defense (3)
- threat and vulnerability management (3)
- ChatGPT (2)
- Evasive loader (2)
- Fileless malware (2)
- Gartner endpoint protection (2)
- financial cybersecurity (2)
- patch management (2)
- Adaptive Exposure Management (1)
- Anti-tampering (1)
- Gartner Emerging Tech (1)
- Healthcare cybersecurity (1)
- IoT security (1)
- Securing IoT devices (1)
- Server security (1)





















.png?width=571&height=160&name=iso27001-(2).png)