Your Guide to Virtual Patching
“Make do and mend.” If you work in IT security, this slogan, from a pamphlet issued by the British government in 1943, probably resonates. In security, constant mending—i.e. patching, is a fact of life. So what is virtual patching and why would you need it?
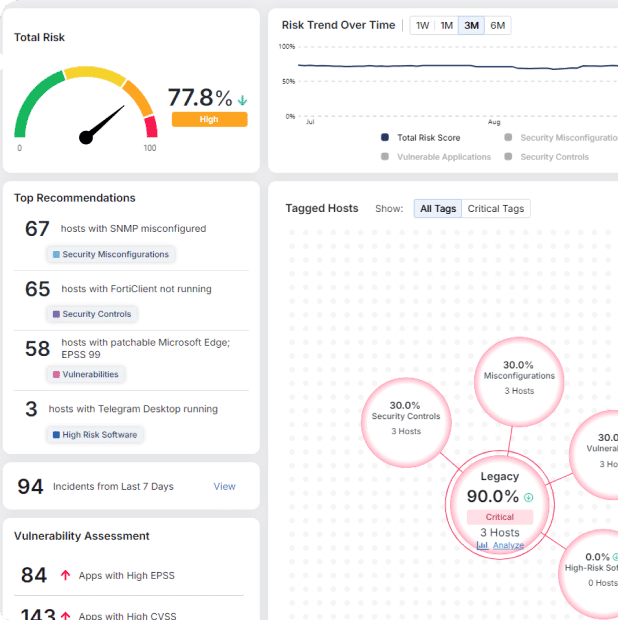
Vulnerability management has been critical since cybersecurity year zero. But the struggle to find vulnerabilities and deploy patches to fix them has become much more complicated. It can be almost impossible for organizations that rely on legacy systems or vast numbers of endpoints to keep on top of critical vulnerabilities. CVE-2017-0199 (patched in 2017) is still one of the most exploited vulnerabilities today.
Virtual patching doesn’t get rid of the need to patch bugs. What it does is protect out-of-patch applications from exploits, giving organizations more time to get applications up to date. For most companies that find patching difficult or, in some cases, impossible, virtual patching can be a security lifeline.
What Exactly is a Virtual Patch?
Virtual patching is a vendor-supplied stop-gap measure for reducing exploit risk. Thousands of firms use it to keep applications with known vulnerabilities safe until they can be fully patched. Technically speaking, virtual patching works by mitigating specific vulnerabilities in applications without changing their code.
Traditional virtual patch solutions like Web Application Firewalls (WAFs) or Intrusion Prevention Systems (IPS) cover specific bugs by spotting and stopping malicious traffic with a customized security layer. They rely on noticing dangers lurking in network traffic and either cutting them off at the source or filtering them away from at-risk applications.
Virtual Patching Has Never Been More Critical
When an organization’s IT suite gets beyond a certain level of complexity, unpatched vulnerabilities are inevitable. Cybercriminals know this—the majority of ransomware attacks exploit unpatched vulnerabilities.
Unfortunately, common vulnerabilities and exposures (CVEs) keep growing faster than defenders can keep up. The number recorded in 2021 was around five times that in 2011. These range from headline-making zero-day vulnerabilities like Log4j, to the thousands of lesser-known vulnerabilities found in legacy applications each year. Keeping up to date with the patches made to counter them is tricky. It doesn’t help that many vendors release updates at the same time every quarter, overwhelming security teams in the process.
All of this means patching takes time, costs money, and doesn’t scale. On average, organizations spend 18,000 hours finding and applying patches each year. Yet even with all of this time spent patching, patch lag (the delay between patch release and deployment) is soaring. The average time to patch a vulnerability is between 60 and 120 days. In some cases, such as patching a medical device, it can take years to deploy a patch.
Patch development also takes precious time, leaving applications dangerously exposed. For example, it took almost 35 days for a patch to become available for the Log4j vulnerability. When Microsoft noted a vulnerability in Exchange in 2021, cybercriminals launched six exploits during the 60 days it took to deliver a patch.

Ironically, sometimes you can patch too fast. One of Morphisec’s clients, Motorola CISO Richard Rushing, told us that taking an aggressive approach to patch management puts him ahead of the vendors he uses. By the time he had patched thousands of endpoints, he was told a vendor’s patch had changed, and repatching was needed. “Patch panic” is common, where firms constantly expend lean resources to implement patches quickly.
Not All Virtual Patches Are Created Equal
The ability to virtually patch applications is a useful resource. But commonly used virtual patch solutions aren’t without problems.
Firstly, solutions like WAFs or IPS rely on spotting malicious traffic. Unfortunately, modern cyber threats, such as human-operated ransomware attacks, don’t behave in predictable ways. Recognizable signatures are often absent.
Because these solutions need to scan high volumes of network traffic, they can also be costly and difficult to manage. When network bandwidth is reduced, they can become ineffective. Infrastructure issues are common.
Perhaps most critically, traditional virtual patch solutions are often slow and difficult to deploy. This is a big problem. For most attacks, the mean time to breach (MTTB) is only five minutes. If it takes you five hours or five days to apply a virtual patch, this gives a cybercriminal time to breach your system.
An effective virtual patch solution takes apart attack pathways. It doesn’t rely on network traffic or signatures to stop threats to out-of-patch devices.
A Better Way of Virtual Patching
Morphisec’s Automated Moving Target Defense (AMTD) technology is faster, more economical, easier-to-implement, and more effective than traditional virtual patching solutions.
MTD doesn’t need to analyze network traffic or spot attack signatures, so it doesn’t impact system performance. Instead, it seals off unpatched vulnerabilities instantly and automatically, requiring no effort, management, or resources. It does this by creating a dynamic attack surface for applications that threat actors can’t penetrate, causing them to abort attacks.
Leading analysts such as Gartner call MTD a “game-changer.” Not only does MTD provide multilayer defense in depth against malware and ransomware, it also protects against zero-day vulnerabilities during the weeks or months before a patch is made available and implemented. To learn more about the benefits of Moving Target Defense and how it works, read the white paper, Zero Trust + Moving Target Defense: The Ultimate Ransomware Strategy.

Stay up-to-date
Get the latest resources, news, and threat research delivered to your inbox.