
On February 22, 2018, Morphisec Labs spotted several malicious word documents exploiting the latest Flash vulnerability CVE-2018-4878 in the wild in a massive malspam campaign. Adobe released a patch early February, but it will take some companies weeks, months or even years to rollout the patch and cyber criminals keep developing new ways to exploit the vulnerability in this window.
All the documents showed a very low detection ratio on VirusTotal and the next stage artifacts were successfully downloaded from a newly registered domain in all cases. Analyzing the attack, it is clear that it took the attackers only a few easy changes to the original targeted attack to outplay static defenses once more.
Note to Morphisec customers: Morphisec prevents all variants of this attack, starting from the first version one and half years ago to this latest one leveraging CVE-2018-4878.
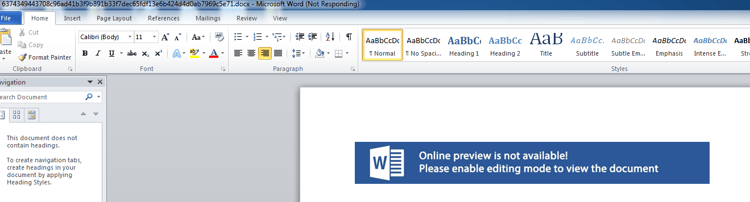
The documents were downloaded from the safe-storge[.]biz domain and went almost entirely undetected with an 1/67 detection ratio.
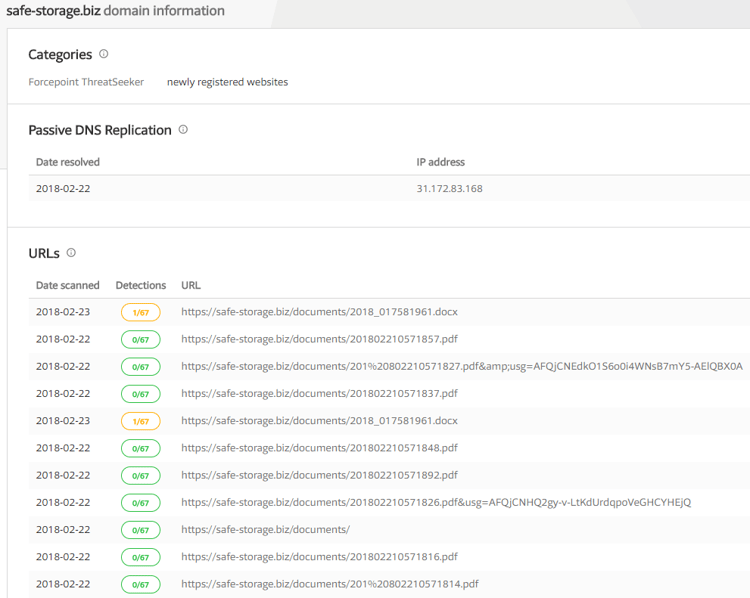
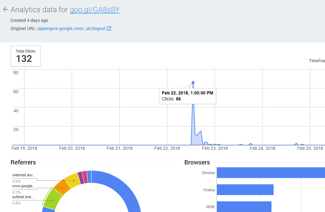
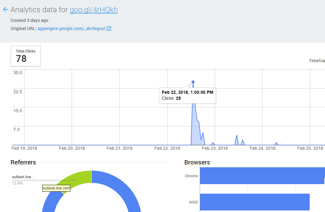
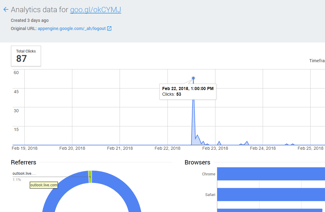
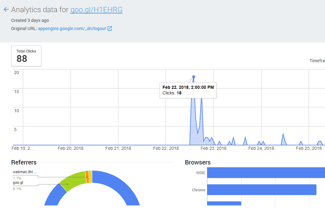
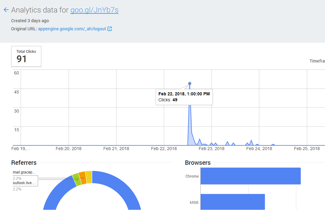
While many security defenses missed their goal, the attack did not. In the emails, the victims received short links to the malicious website generated by Google URL Shortener. This gives us the ability to see the analytics for the short links, such as click rate and mail host used. For example, we see that victims opened it through Outlook, Gmail and the Italian WebHost Aruba.it. This is of course only a partial picture; we detected five different short links, but there are likely more.
The analytics for the short links shows the same pattern as legitimate email campaigns. Clickthroughs spike in the first couple of hours after emails are sent. Signature-based defenses, like antiviruses, cannot cope with this pace.
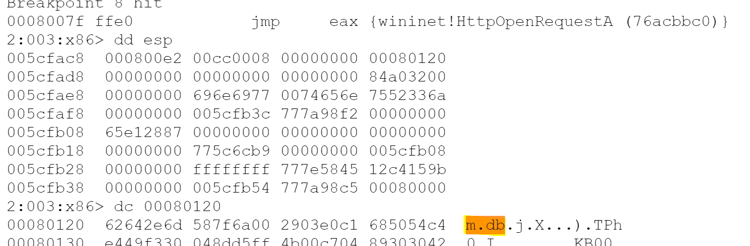
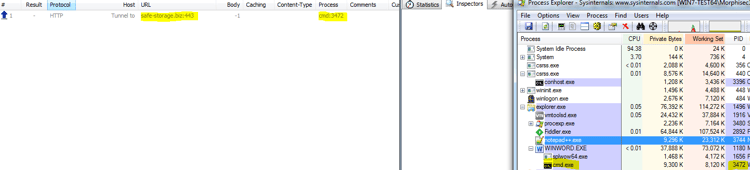
After downloading and opening the Word document, the attack exploits the Flash vulnerability 2018-4878 and opens a cmd.exe which is later remotely injected with a malicious shellcode that connects back to the malicious domain.
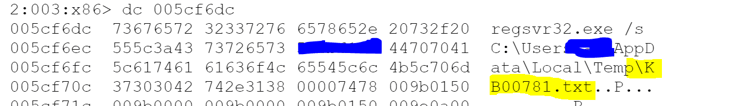
In the next step, the shellcode downloads a "m.db" dll from the same domain, which is executed using regsvr32 process in order to be able to bypass whitelisting solutions:
Regsvr32 Process:
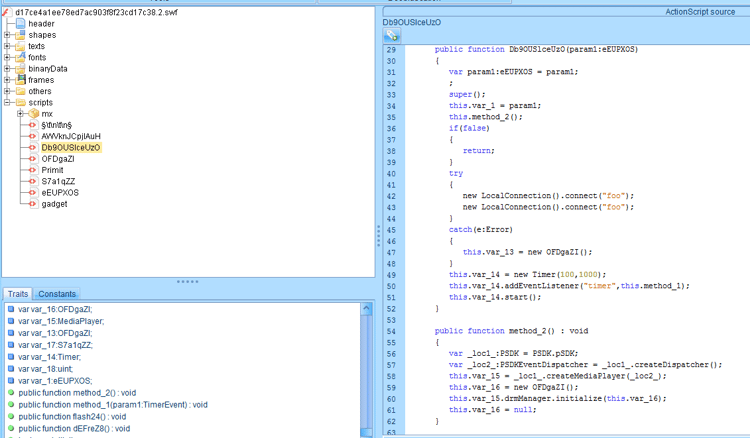
Also the extracted SWF Flash file had very low detection score on VirusTotal:
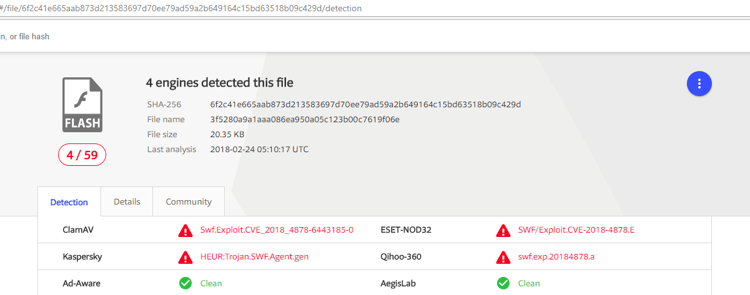
The disassembled Flash file had a very similar signature to existing PoCs, especially to the stripped 32 bit PoC. Unlike the original attack, however, the current malspam campaign doesn't have a 64 bit implementation.
Conclusion
As expected and predicted, adversaries have quickly adopted the Flash exploit, which is easily reproducible. With small variations to the attack, they successfully launched a massive malspam campaign and bypassed most of the existing static scanning solutions once again.
Morphisec's Endpoint Threat Prevention solution is agnostic to the morphing and obfuscation of the exploit, and prevented the exploit before any damage could occur.
Artifacts:
|
Artifact |
Sha2 |
|
2018_017581961.docx |
6374349443708c96ad41b3f9b891b33f7dec65fdf13e6b424d4d0ab7969c5e71 |
|
activeX.bin |
eaf0f57cbcbda0dbd2c60c5719731ddeab76b6a10367d2679854202fdca27388 |
|
activeX.bin |
176ad6129ece312f128a3195bf5afc130801f2e849f89bc97610c1ce8d730772 |
|
SWF |
6f2c41e665aab873d213583697d70ee79ad59a2b649164c15bd63518b09c429d |
|
<unknown name>.docx |
862c6ef1d24d2cba9878b5e919683629c3516d9121f5cf703ff1ca42e2a06a77 |
Domain: safe-storage[.]biz:443
Short Links:
goo[.]gl/okCYMJ
goo[.]gl/4rHQkh
goo[.]gl/GA8sBY
goo[.]gl/H1EHRG
goo[.]gl/JnYb7s





.png?width=571&height=160&name=iso27001-(2).png)