Gartner has released new research about moving target defense (MTD) that we want to bring to your attention. Their findings demonstrate why MTD is a vital component of a prevention-first cybersecurity strategy. [2023 UPDATE: New Gartner report states that “Automated moving target defense is an emerging game-changing technology for improving cyber defense."] Likewise, their forecasts predict rapid MTD adoption by vendors and security teams in the near future. Above all, Gartner’s findings about MTD validate the mission Morphisec is on: leveraging the power of moving target defense to defeat modern cyber attacks, especially those that haven’t been seen before, and thereby bringing peace of mind to IT and security professionals.
How Gartner Defines Moving Target Defense
“Moving target defense (MTD) is a technology trend whereby dynamic or static permutations, morphing, transformations, or obfuscations are used to deflect attacker exploitation techniques.”
This definition also describes what Morphisec does. Morphisec’s breach prevention solution leverages the power of its patented Moving Target Defense technology to STOP advanced attacks through the zero-trust approach within the perimeter - we implement MTD to deflect attacks on application runtime by hiding the attack surface. Morphisec’s MTD also provides credentials protection on the endpoint by shuffling the credentials structure in parallel. Complementary MTD techniques are applied on application resources to minimize the attack surface on user account management.
Why Moving Target Defense Works
“Assume an expert thief is able to pick the lock to any door. The goal of MTD is not to build a better lock. This is, without doubt, a laudable and necessary goal for improving the door’s security, but this mission is left to other security solutions. Instead, the goal of an MTD security strategy is to make the door and the door’s lock difficult or impossible for the thief to find.”
Moving target defense works by moving assets from where hackers think they will be to an unknown location. When an attack can’t find what it intends to exploit, it becomes benign as a result. By upending expectations and keeping sensitive assets hidden, MTD successfully deflects attacks and prevents (rather than mitigates) the damage.
Adding to the defensive capabilities, MTD works against unknown zero-day and fileless malware attacks, in-memory exploits, and other threats that even the most advanced endpoint detection and prevention tools cannot catch. Since MTD does not rely on attack signatures to identify threats, like next-generation antivirus (NGAV) tools, or need to detect malicious intent to neutralize these, such as endpoint detection and response (EDR) solutions, it stops old and new threats with equal proficiency.
Why Moving Target Defense Matters
“Attacker exploitation techniques rely on predictability of vulnerabilities in software, systems, system services or applications when executing attacks. For example, an attacker must author exploitative code to target a specific area of stored data in memory, use a known application runtime parameter, or utilize parsing of web application code to execute exploits against these elements.”
One of the few things nearly all cyber attacks have in common is reliance on a precise plan of attack. Throwing a wrench into those plans makes for a logical and powerful defensive tactic at a time when cyber risk is rising fast. Companies are more vulnerable than ever as their tech footprint grows and the attack landscape gets worse, and with cyber breaches capturing monthly headlines, there’s only one conclusion: it’s time for new thinking about cybersecurity tools and techniques. MTD offers a fresh perspective on both.
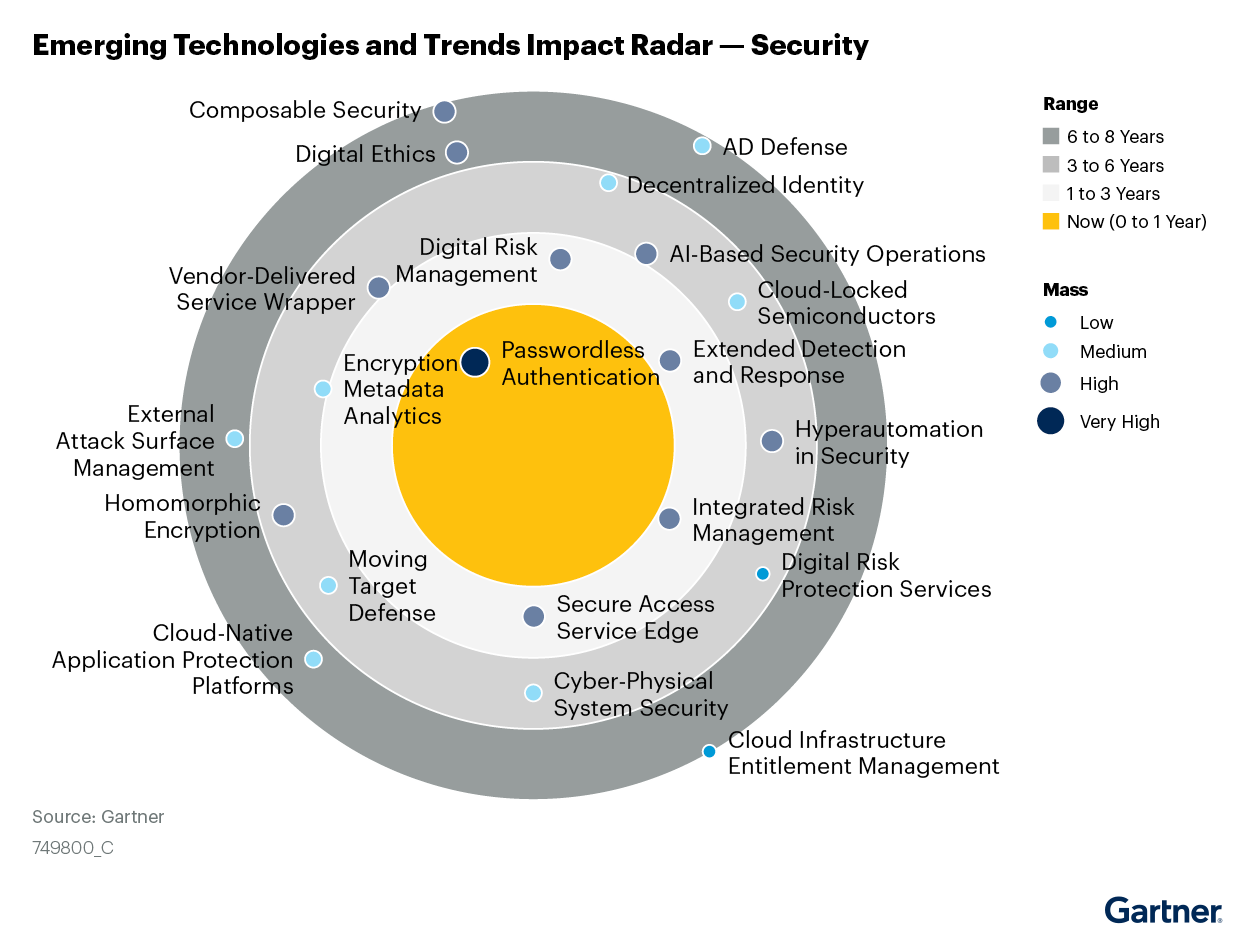
In fact, in a recent report, Gartner identifies the most impactful emerging technologies driving innovation in the security market, citing Moving Target Defense as a key technology for improving security across memory, network, applications and operating systems. (refer to Figure 1 below)
What Makes MTD Different?
Gartner highlights three distinct benefits of MTD compared to other methods for vulnerability assessment and management:
- Accessible – Implementing MTD requires little refactoring or disruption, especially when applied at the endpoint or application-level where “the use of MTD techniques is immediately achievable.”
- Complementary – MTD tools are not a replacement for existing security solutions but rather a complement that adds important defenses without creating redundancies or performance issues.
- Scalable – Since MTD tools deflect attacks, security teams have less to detect and respond to, making it easier to scale up systems without becoming overwhelmed by the security requirements.
Beyond the technical benefits of MTD, it represents a new (overdue) approach to cybersecurity based on the reality that no one can fix every security vulnerability or stop every threat. Instead, they must supplement those efforts with what Gartner describes as ”the pragmatic nature of “deflecting” attacks in order to keep up with the level of modern cyber threats.”
Today’s security teams can’t expect to see or stop every attack at the defensive perimeter, so they need security layers inside that perimeter to protect sensitive assets (like the application memory) commonly under attack. That way, even if an attack succeeds at a subsequent security level, it fails upon reaching the final target thanks to the evasive maneuvers applied by moving target defense.
The Future of MTD According to Gartner
“By 2025, at least 30% of commercial network, host and software security solutions will incorporate moving target defense techniques/technologies, up from less than 5% today.” [2023 UPDATE: New Gartner report states that “Automated moving target defense is an emerging game-changing technology for improving cyber defense."]
Gartner expects MTD to spread fast for two reasons. First, security vendors are likely to integrate MTD into existing and emerging security platforms, both to upgrade those platforms and distinguish them from the competition. Second, companies like Morphisec will continue innovating in this space, making moving target defense increasingly accessible and formidable. In either case, customers will flock to these solutions seeking advanced defenses against aggressive and sophisticated cyber attacks.
Morphisec – On the Leading Edge of Cybersecurity
Morphisec, as the leader in Automated Moving Target Defense, has proven the power of this technology. We have deployed our MTD-driven breach prevention solution at over 7,000 enterprises, protecting over 8 million endpoints and servers daily from many of the most advanced attacks. In fact, Morphisec is currently stopping 15,000 to 30,000 ransomware, malware, and fileless attacks per day that NGAV, EDR solutions and endpoint protection platforms (EPP) have failed to detect and/or prevent. (e.g., Morphisec customer success stories, Gartner Peer Insights reviews and PeerSpot reviews) Examples of such attacks that were stopped at day zero, when other NGAV and EDR solutions were unable to stop them, include but are not limited to:
- Ransomware (e.g., Conti, DarkSide, Lockbit)
- Backdoors (e.g., Cobalt Strike, other in-memory beacons)
- Supply Chain (e.g., CCleaner, Asus, Kaseya payloads, Itunes)
- Malware Downloaders (e.g., Emotet, QBot, Qakbot, Trickbot, Icedid)
Read Gartner’s “Emerging Technologies and Trends Impact Radar: Security” here to learn more about the power of Moving Target Defense. And to learn more about how Morphisec uses Moving Target Defense to provide end-to-end protection against the most damaging cyberattacks, visit: https://www.morphisec.com/products/.
References
Gartner Emerging Technologies and Trends Impact Radar: Security, Ruggero Contu, Mark Driver, Lawrence Pingree, Elizabeth Kim, John A. Wheeler, Swati Rakheja, Nat Smith, Mark Wah, Dave Messett, Shawn Eftink, Bill Ray, 12th October 2021
This graphic was published by Gartner, Inc. as part of a larger research document and should be evaluated in the context of the entire document. The Gartner document is available upon request from Morphisec.
Gartner does not endorse any vendor, product or service depicted in its research publications and does not advise technology users to select only those vendors with the highest ratings or other designation. Gartner research publications consist of the opinions of Gartner's Research & Advisory organization and should not be construed as statements of fact. Gartner disclaims all warranties, expressed or implied, with respect to this research, including any warranties of merchantability or
fitness for a particular purpose.








.png?width=571&height=160&name=iso27001-(2).png)