
In the past month, Morphisec has investigated the origin of several increasingly prevalent infostealers. These include Redline, Taurus, Tesla, and Amadey.
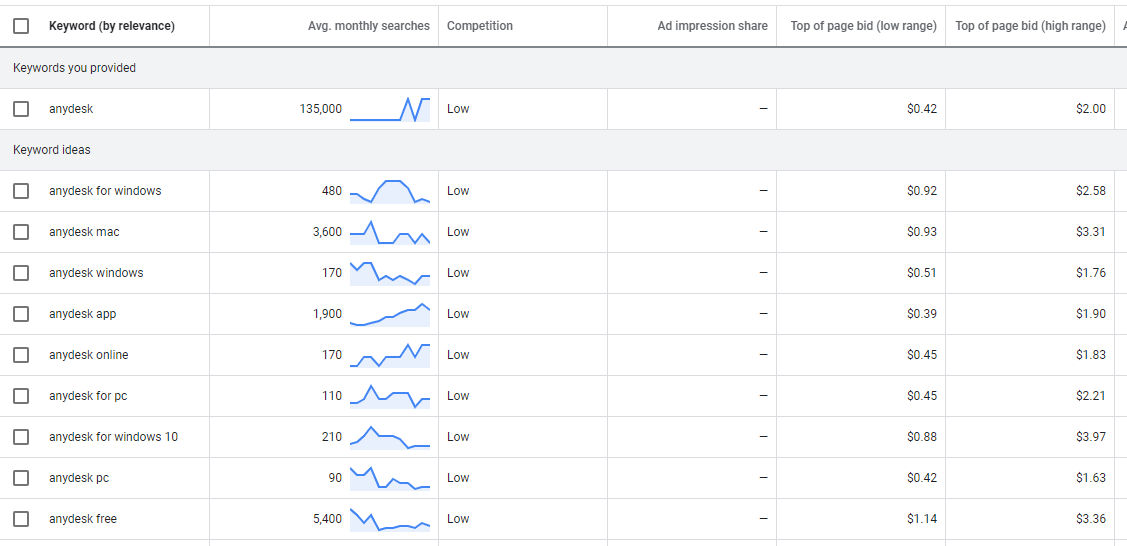
As part of our research, we identified pay-per-click (PPC) ads in Google’s search results that lead to downloads of malicious AnyDesk, Dropbox and Telegram packages wrapped as ISO images.
The PPC ads targeted specific IP ranges in the US and probably some other countries. Non-targeted IPs are redirected to legitimate pages that download the correct applications.
The advertisements being on the first page indicates the need for constant vigilance on all levels. Adversaries will clearly take all opportunities possible to target their chosen victims, even going so far as to use legitimate services such as Google Adwords.
In this threat post we will go through three attack chains that lead to Redline, Taurus and a new mini-Redline infostealer compromise. We will focus on two adversaries because of similarities in patterns, certificates, and C2s. The first adversary leverages Redline and the second uses Taurus and mini-Redline.
We will cover Amadey in a separate blog post.
Technical Introduction
All of these attack chains start with one of a dozen paid Google ads that lead to a website with an ISO image download. The ISO image size is larger than 100MB, which allows the image to evade some scanning solutions that are optimized on throughput and size.
Mounting the ISO image leads to executables that are usually, but not always, digitally signed and legitimately verified.
Adversary One delivers the Redline infostealer.
- .Net executables are obfuscated with known obfuscators such as DeepSea, which leads to a custom obfuscated .Net DLL loader that eventually leads to a custom obfuscated Redline stealer .Net executable.
Adversary Two delivers Taurus and a mini-Redline infostealer.
- Taurus AutoIt - 7fx executables that recreate and execute a legitimate AutoIt compiler with a malicious AutoIt script and a malicious encrypted Taurus executable that will be hollowed into the AutoIt process.
- Mini-Redline - A minimized .Net version of the Redline stealer with some common functionality for stealing data from browsers. It features different configuration and communication patterns wrapped in four layers of obfuscation.
Redline Infostealer
As can be seen from the image below, a simple search for “anydesk download” leads to three pay-per-click Google ads. All three lead to malicious infostealers. . The first 2 advertisements lead to a Redline stealer while the third one leads to the Taurus infostealer.
TheRedline infostealer websites are signed by a Sectigo certificate, as seen in the image below.
Double Clicking the download button on any of the websites will lead to a script execution that verifies the IP and delivers the artifacts from one remote website “hxxps://desklop.pc-whatisapp[.]com/”.
The artifacts are updated and re-uploaded to the website every couple of days.
As mentioned before, every ISO file includes a very small .Net executable. In some cases, this executable is also digitally signed.
The first layer of the executable is obfuscated with DeepSea.
The second layer is actually a custom obfuscated .Net DLL that executes in memory.
Finally, the third layer is the well known Redline infostealer. It communicates back with jasafodidei[.]xyz:80.
As the infostealer is well covered by other researchers, we decided to end with a snapshot showing the variety of databases this infostealer targets. Surprisingly, this infostealer targets browsers that are also used in Russian-speaking countries
Taurus Infostealer
The Taurus infostealer is delivered in a similar way and appears as the third paid ad in a search for the popular applications mentioned in the introduction.
This time the website is signed with a legitimate Cloudflare certificate. Like the Sectigo certificate used with Redline, the Taurus certificate is not older than two weeks
In the Taurus case, we did not see any redirects to additional websites. As can be seen in the image below, the download results from a submitted form that is handled by “get.php” and in turn delivers the ISO image directly from the website.
If the target is not within the range of interesting IP addresses, users will see a normal redirect to the legitimate application website like in the Redline infostealer.
The downloaded ISO image consists of a 7z SFX executable.
The executable includes either 4 “flv” or 4 “bmp” files in the examples we cover below. Sfx is configured to start the execution from the first batch file (masquerading as either flv, bmp or any other unique extension). The batch script is then redirected as input into cmd.exe.
This batch script is well documented. It is responsible for the re-creation of the legitimate AutoIt compiler (Ali.exe.com or the Dio.exe.com in the examples above) and the execution of the malicious AutoIt script (Pramide.flv or the Debbano.bmp). Through the re-created compiler, it will fail to execute upon detection of a known sandbox provider. A VirusTotal search for additional 7z SFX archives with a similar evasion will lead to more than 400 different files uploaded in the past month.
The AutoIt script supports both 32 and 64 bit processes (slightly deobfuscated).
It also implements persistence through a URL link directly in the startup folder. The link executes Javascript from a hidden folder under roaming (use attrib -H to unhide).
As in the previous batch file execution, the Javascript file executes the AutoIt compiler with the copied Taurus AutoIt script.
Mini-Redline Infostealer
As with the Taurus campaign, the advertisement websites that lead to the mini-Redline infostealer are also signed with Cloudflare certificates.
The file inside the ISO is also padded with zeros to increase the size of the file for evasion purposes.
The executable is a .Net assembly with an unknown obfuscation pattern; dynamic unpacking of the assembly reveals four (4) layers of obfuscation and hollowing.
First Layer
Second Layer
Third Layer
Fourth Layer - Hollowed Mini-Redline
Finally, the last layer leads to some known stealing functionalities. An initial static look at the file is reminiscent of Redline; not surprisingly a VT scan for the unpacked file shows that it will confuse even the biggest security vendors. The method and strings implemented as part of the Chrome credential theft are almost identical. In both cases, the databases are copied to a temporary location before being decrypted, using similar methods and class names to do so even though the number of targeted browsers is minimal.
Nevertheless, the communication pattern is different. Mini-Redline uses a direct TCP socket connection.
Some of the anti-debugging functionalities include “DebuggerHidden” attributes and virtualization detection.
Virtual Environment evasion checks using WMI.
Conclusion:
Adversaries will use any method possible to gather targets, even paying Google top dollar for their paid search results to surface a malicious website as a top search result. This inventiveness on the part of threat actors means that organizations need to be constantly vigilant in all aspects of their operations. There’s no telling when an adversary will set up a website with a signed, legitimate certificate designed to mislead website visitors.
Thankfully, Morphisec customers are protected against these infostealers through our zero trust at execution technology powered by moving target defense.
URLs Redline Infostealer
hxxps://me.anydesk-pro[.]com/
hxxps://desklop.telegram-home[.]com/
hxxps://pc.anydesk-go[.]com/
hxxps://desklop.anydesk-new[.]com/
hxxps://desklop.pc-whatisapp[.]com/
URLs Taurus and Mini-redline Infostealer
hxxps://anydesk-en-downloads[.]com/
hxxps://anydesk-one[.]com/
hxxps://anydesk-top[.]com/
hxxps://anydesk-connect[.]com/
hxxps://anydesk-vip[.]com/
C2 - Redline infostealer
jasafodidei[.]xyz:80
ISO - Redline infostealer zip files
C249E79B05D3385A50BD0D54881B59BD
76118B65F29856DB2ABECD1193D08CF1
ISO - Taurus
476A504DB16C7E6972775B1160B4631C
F0EF3E84F172C8E869088F1FCF933B07
7DAB7515FC7C795A2AD2BD8D22F36A14
ISO - Mini-Redline
7B91DF7AF3BC0CFACFF46DB883BA784D
Taurus and Mini-Redline C2
109.234.37[.]201:15647




.png?width=571&height=160&name=iso27001-(2).png)