
In the last 48 hours, a hurricane of e-mails has crossed my Inbox, with breathless and self-congratulatory subject lines like "Our latest release detects Bad Rabbit" and "XYZ now protects XYZ customers from Bad Rabbit." In other words, "If you use our product, you were exposed to Bad Rabbit, but now that we know about it (from someone else) we deployed an update." Once you decode the messages, it’s clear that the content is not newsworthy, differentiating or exciting, it’s just an excuse to partake in the latest frenzy.
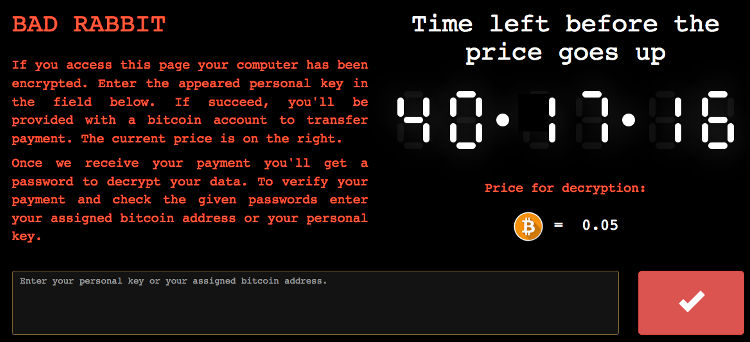
Any endpoint security product can protect against any attack if someone tells it what the attack looks like and where to find it. But in the time it takes for that to happen you might well find your data encrypted and a ransomware notice on your screen.
So did anyone prevent Bad Rabbit ransomware BEFORE the headlines and emails popped up? Without the need to know anything about the attack – without even detecting it in fact?
If they did, they'd be the go-to product, the one that can protect you from future attacks.
Does this defy the natural laws of cyber? Nope. It's a matter of finding a way to combat adversaries' advantages of unpredictability and access to ever-advancing in-memory attack technology. Morphisec dynamically morphs the run-time environment, making the memory structure unknowable to attacks. Attackers’ 'maps' of predictable defenses, system resources and vulnerabilities become obsolete and no longer guide them to the resources they are designed to exploit. And just to make things a little more inconvenient for the hackers, every attack is instantaneously trapped and prevented.
So does Morphisec detect Bad Rabbit ransomware? Yes. But the way it does it is unremarkable, business as usual. Without fanfare, alerts, or pressure-cooker case management, the attack was terminated. Effortlessly, without updates. In fact, the very first version of Morphisec prevents Bad Rabbit ransomware and almost all the other attacks you read about. Morphisec's prevention mechanism does not need to be updated as attack techniques evolve. Regardless of technique, the attack needs a map to get to an exploitable resource in the vital and largely unprotected layer of memory. And Morphisec doesn't give it the new map.
This is unremarkable in the sense that Morphisec works silently and reliably, with no chest thumping, to nullify the deadliest arsenals of advanced threats. On the other hand, maybe it is remarkable.




.png?width=571&height=160&name=iso27001-(2).png)