
This report was authored by: Michael Gorelik and Assaf Kachlon.
Last week’s malware news was filled with the CCleaner backdoor exposed by Morphisec’s security solution. This week Morphisec uncovered another ongoing malware campaign, this one a drive-by-download attack that uses a modified version of the old (in hacker time) favorite, the RIG exploit kit.
RIG
First appearing in 2014, RIG generally uses gates to redirect victims from a compromised website to a landing page that contains the EK, exploiting vulnerabilities in JavaScript, Flash and VBscript in the infection chain.
Over the past 10 days, Morphisec's Threat Prevention Solution stopped a modified RIG exploit kit distributed to a large number of customers in a major drive by download campaign.
Upon customer notification about the web-borne attack, we immediately identified the type of exploit kit and the delivered exploits. We reported the abuse of the registered domains to Freenom.com, the domain registration entity.
The past several months had seen a dramatic reduction in the drive-by-download attack vector, which has been mainly dominated by the RIG exploit kit. A major takedown operation between February and May of this year affected operations significantly.
Now, however, they seem to be back in play. Earlier this month Malware Bytes reported a campaign that used RIG to deliver Princess ransomware. The RIG campaign discovered by Morphisec delivers Smoke Loader and Miner, which include evasive techniques to persist in registry.
Technical details
During the investigation of the prevention logs, we identified the IPs and domains to deliver the exploit kit. It was a single domain - camp200917[.]gq – that triggered our interest.
Although the domain name was freely registered, it obviously hints at a campaign of a targeted nature. We decided to verify whether additional top-level domains have been registered with the same name. While hunting for additional free domain registrations we found "Freenom.com". Surprisingly all the top-level domains available through the Freenom service related to camp200917 have been registered and most of them were pointing to the same IP:
camp200917[.]ml => IP1, camp200917[.]tk => IP1, camp200917[.]cf => IP2, camp200917[.]gq => IP1, camp200917[.]ga -> IP2.
At the moment of writing this blog camp200917[.]cf and camp200917[.]ga are still very active and deliver Flash, JavaScript and Silverlight exploits.
The currently active domains are forwarding to the RIG gate 5[.]23.49.9 and 92[.]53.104.143…, although we observed other IPs as well.
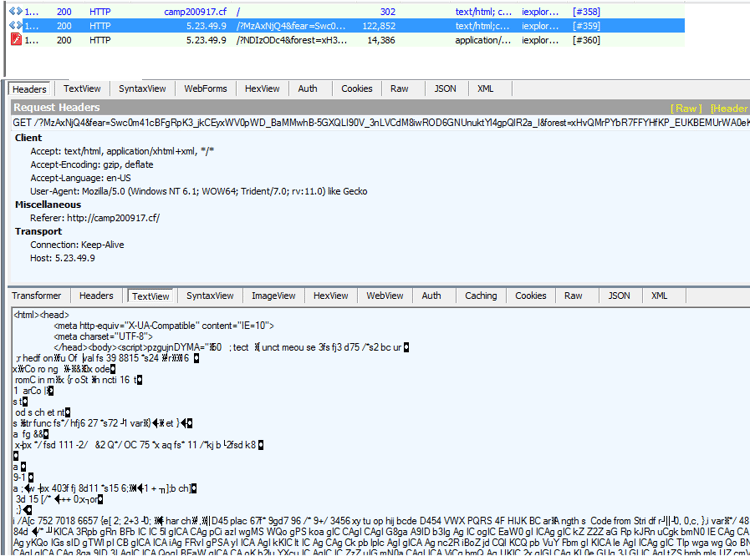
NEW RIG PATTERN
The new RIG pattern observed in this campaign is:
- ?MzAxNjQ4&
- fear=Qwc0m41cBFgRpK3_jkCEyxWV0pWD_BaMMwhB-5GXQLI90V_3nLVCdM8iwROD6GNUnuktYl4gpQlR2a_I&
- forest=xQvQMrPYbR7FFYHfKP_KBKBEMUrWA0eKwY2Zha3VF5qxFDTGpbL1FxzspVydCFyEmvZvdLcHIweh1UbA&
- sara=MjI3NTUyODU=
- /?NDIzODc4&
- forest=xH3QMrXYbRrFFYbfKP_EUKdEMUzWA0OKwY-Zha_VF5yxFDTGpbL1FxjspVidCF6EmvBvdLAHIweh1UfASwE&
- fear=0m4tcBF4RpKv_jkWEyxeV0pWD_BCMMw5B-5eXQLQ90Vz3nLVCdM8iwROD6GNUnustUVkR4QgTnqz7VaKO-w&
- land=ODUzMjQxOA==
- /?NTY3Mzcw&
- fear=SwRhmIoMA15G9q37jUTSnBOd05TWqRePMwhD_pDBFrJp21_zx7BHcMkmlBeEu2ABzuktYlggpQlR2a_I&
- forest=xHvQMrXYbRvFFYffKPrEUKdEMU7WA0SKwY2ZhazVF5yxFDfGpbL1FxzspVydCFyEmvJvdLEHIwKh1UTA&
- moon=NDYxMDY5NDU=
- /?MTU0MTk3&
- fears=3yIsLBl5ApKj920SGmhOcgpWLqBCNZAkT95CXFrNo3Fn0xrUSdMoklhSE6WIBmOktW1kW5AgSnav7VaSO-w&
- forests=xHzQMrPYbRrFFYbfKP_EUKdEMU7WA0OKwYyZhazVF5yxFDXGpbD1Fx_spVydCF6EmvdvdLMHIwah1UTASwE&
- lands=NDM5MTY2NTY=
- /?NjA3NDcx&
- forests=xX3QMvWebRXQCZ3EKv_cT6NBMVHRHkCL2YudmrHSefjaeVWkzrbFTF_xozKASwSG6_ZtdfJ&
- fears=VDVW1jBPUKAcyz9tZAQkT8qun20LVzECdiJWA_kaJYAlM-ZaUF-A93V2km7AkQPslg1TH7GI&
- saras=MjE2OTg2NDg=
Earlier the same week we observed additional parameter triplets, such as sea, warm, damn and others.
PERSISTENT SMOKE LOADER /MINER:
The downloaded Trojan (e.g. 4cad28b1f8b20f75df5e93eff725de093c4a6b660b5faf84938214cfad131e89) is written to temp directory (local/temp). As a first step, it kills and disables some forensic tool processes (e.g. process explorer, Wireshark). Later it injects into a number of processes and persist itself through registry.

CONCLUSION
Morphisec Endpoint Threat Prevention solution prevented the attack without the Trojan ever being downloaded to disk. Separately we investigated whether Morphisec would also prevent the Smoke Loader executable. As expected, Morphisec also prevented the loading of the executable before any damage could occur.
Morphisec’s patented Moving Target Defense technology prevents this attack in particular across its entire attack chain, but also in general prevents web-borne attacks without any prior knowledge of signatures, patterns or behaviors.




.png?width=571&height=160&name=iso27001-(2).png)