
This article is the first in a three-part series looking at Morphisec version 3.5 - Unified Threat Prevention platform. Next week we take a deep dive into the new Attack Trajectory and the ways that this powerful tool can be used. Subscribe to this blog to receive notifications when the rest of the series goes live!
Organizations struggling to balance the necessity for protection from advanced cyberthreats against the very real requirements to simplify their security operations and stay within budget, just got handed a sizable new weapon. Morphisec has announced version 3.5 of our Unified Threat Prevention Platform, which makes it easier for companies to replace legacy AV with a far more secure alternative at no additional cost. At the same time, the new Morphisec Unified Security Center provides end-to-end visibility across all blocked attacks so security teams can better understand and address the threats their organization faces.
End to End Visibility with Morphisec Unified Security Center
The latest version of Morphisec unveils the new Morphisec Unified Security Center, which gives security teams a deeper understanding of how their organization is being attacked, putting unprecedented attack detail at their fingertips. Users can see the entire attack timeline and what TTPs adversaries are using at each stage, along with critical data points such as certificates, hash, integrity level and command line instructions.
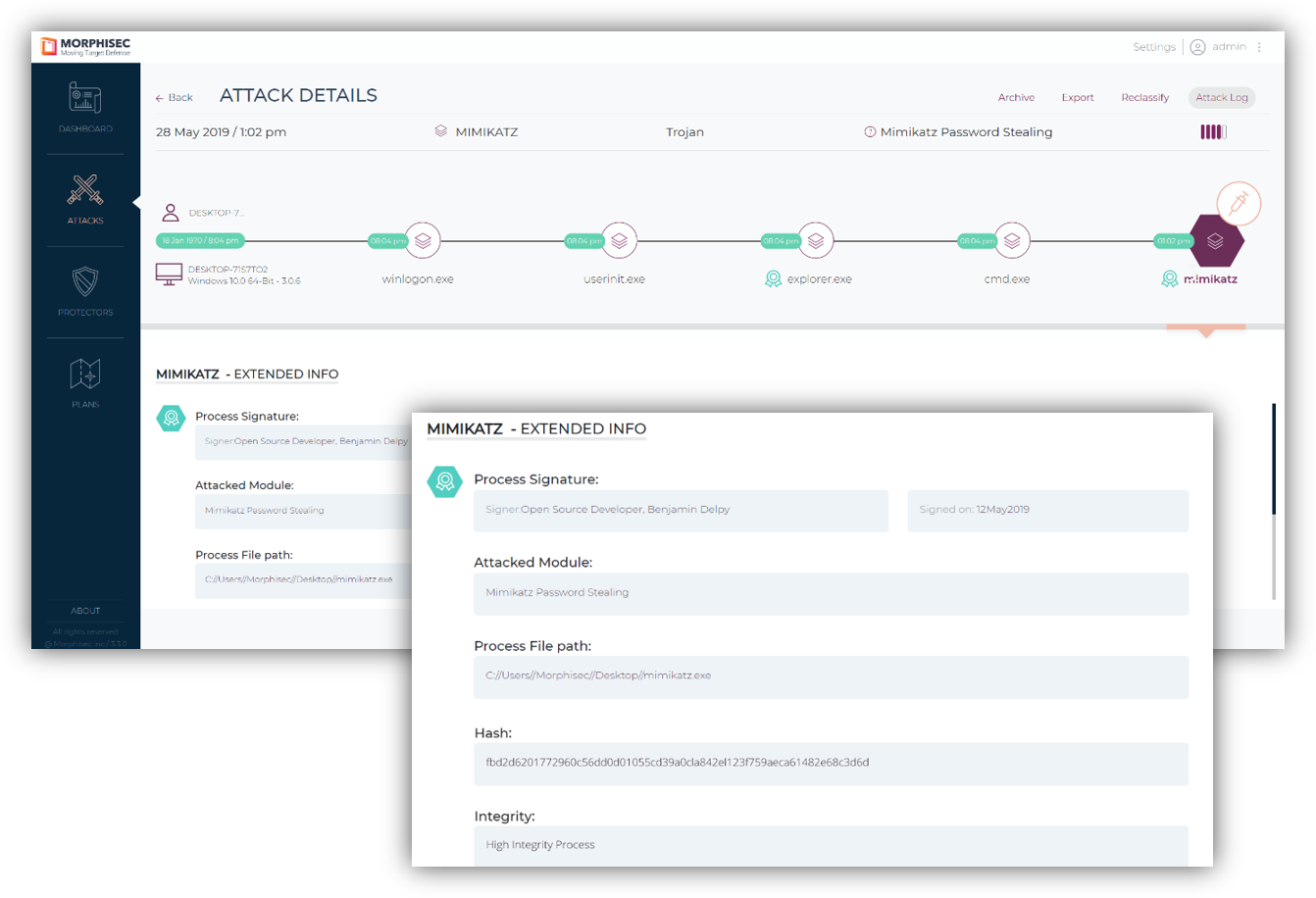
This helps security teams to visually understand the story of the attack and its impact. They can trace it back to its point of origin or, for an attack that was already in residence before Morphisec was deployed, determine how it maintains persistency. This enables security teams to determine what actions they may need to take both on the attacked endpoint and across the enterprise.
Replace Legacy AV with Morphisec-Strengthened Microsoft Defender AV
Morphisec’s latest version includes a new Morphisec Defender AV integration that allows enterprises to better leverage the embedded security features in the Windows 10 operating system. More than 200 million enterprise workers now use Windows 10 and this is expected to increase sharply after Microsoft ends support for Windows 7 in January 2020. Enterprises have a unique opportunity to replace their legacy antivirus tools with the free, embedded Microsoft Defender AV, however the tool’s lack of comprehensive reporting has been a major obstacle to adoption.
Morphisec’s new-Defender integration changes this. Morphisec now provides a consolidated view of all attacks on the endpoint, including real-time attacks detected by Defender AV. Organizations can adopt Defender AV, and use Morphisec to see all Defender AV activity along with the severity level. Security teams can correlate these events with Morphisec prevented threats to understand the impact of the events on the enterprise and make any necessary policy or remediation decisions. For example, a more restrictive Morphisec policy can be imposed on endpoints that are identified as highly targeted.

This means that organizations seeking to strengthen their security posture, without increasing cost and complexity, can scrap their legacy antivirus, turn on the Windows 10 embedded Defender AV, and apply their savings to Morphisec to protect against advanced memory-based attacks that are able to bypass detection-based security tools.
Additional Features
The new Morphisec release also brings across the board upgrades and enhancements including expanded attack classification capabilities, extended cyber prevention mechanisms and security and performance enhancements.





.png?width=571&height=160&name=iso27001-(2).png)