If you have anything to do with cyber security, you know it employs its own unique and ever-evolving language. Jargon and acronyms are the enemies of clear writing—and are beloved by cyber security experts. So Morphisec has created a comprehensive cyber security glossary that explains commonly used cybersecurity terms, phrases, and technologies. We designed this list to demystify the terms that security professionals use when describing security tools, threats, processes, and techniques. We will periodically update it, and hope you find it useful.
Test your cyber knowledge!
Quiz Results
Your Score: 0/
The A-D of Cyber Security Terms
A
Access control
A security process that regulates who can and can’t view sensitive data or resources. It comprises two parts: authentication and authorization (see below).
Account takeover
An attack where a cybercriminal gains access to a legitimate account through stolen credentials. The cybercriminal can then use this access for financial fraud, data exfiltration, internal phishing attacks, and more.
.jpg?width=1000&height=667&name=shutterstock_1303790830%20(1).jpg)
Advanced persistent threat (APT)
A targeted and sustained cyber-attack. Executed only by highly sophisticated attackers and nation-states who aim to remain undetected in a network for as long as possible. APTs can have different goals, including cyber espionage, financial gain, and hacktivism.
Alert fatigue
When security professionals receive so many security alerts they become desensitized to them. Alert fatigue can result in security teams missing or ignoring important alerts.
Allow-list
A list of IP addresses, domains, applications, and email addresses with privileged access. Everything and everyone that is not on an allow-list (sometimes also known as a whitelist) is denied by default.
Antivirus (AV)
A type of software program that scans for and removes malware from devices.
Learn more: Why AV and EDR Are Failing and How to Better Secure Your Company

Application controls
A cybersecurity technology that prevents the installation and execution of unauthorized applications.
Assume breach
A cybersecurity strategy based on the assumption that an organization is already breached or will be breached.
Attack path
A visualization of the chain of vulnerabilities an attacker exploits to infiltrate an organization.
Attack surface
The sum of an organization’s IT assets exposed to threat actors, whether knowingly or unknowingly, and that could offer entry into an organization.
Attack vector
A method an attacker can use to gain unauthorized access to an IT infrastructure. Attack vectors are also known as threat vectors. Common attack vectors include compromised credentials, insider threats, and phishing.
.jpg?width=1000&height=667&name=shutterstock_2118942314%20(1).jpg)
Authentication
A way of guaranteeing users are who they claim they are. Authentication usually happens in conjunction with authorization (see below) and is part of access control (see above).
Authorization
A method of determining whether a user should receive access to sensitive data or resources. Authorization is usually paired with authentication (see above) and is part of access control (see above).
Automated Moving Target Defense
Technology that randomizes application memory runtime, obfuscating targets so threat actors can’t find them.
Learn more: Why You Should Care About Moving Target Defense
B
Backdoor
An unauthorized way to access a computer system that bypasses the system’s security measures.
Backup
A copy of a system’s data. Having a backup means you can restore your data if it’s lost or stolen.

Banker Trojan
A type of Trojan malware that steals sensitive information from a banking institution’s clients.
Learn more: Can Banks Keep Winning Against Advanced Cyberattacks?
Baselining
Figuring out what normal behavior is in your network. Baselining makes it easier for organizations to recognize abnormal activities.
Behavioral analysis
A security methodology that spots anomalies by using big data, artificial intelligence, machine learning, and analytics to understand the behaviors of users and entities in an IT environment.
Black box testing
Testing a system without any prior knowledge of how the system works internally.
Black hat
Criminals who hack into systems for malicious purposes.
Blue team
Security professionals whose job is to defend an organization from cyber-attacks.
.jpg?width=1000&height=563&name=shutterstock_1036755457%20(1).jpg)
Botnet
A network of internet-connected devices that are infected by malware and controlled remotely by threat actors. Cybercriminals use botnets to perform distributed denial of service attacks (DDoS—see below), send spam, and mine cryptocurrencies. Many, if not most victims have no idea their IT assets are part of a botnet.
Bring-Your-Own-Device (BYOD)
A policy that allows employees to use personal devices instead of company devices to connect to an organization’s network and access business applications and data.
Brute force
A trial-and-error hacking method to guess login information and encryption keys. Cybercriminals try all possible character combinations until they can authenticate one.
Bug
A software or hardware vulnerability threat actors can exploit to gain unauthorized access to a system.
Bug bounty program
Initiatives set up by organizations that encourage individuals to look for and disclose software vulnerabilities and flaws for a reward.
Business email compromise (BEC)
An email scam where cybercriminals pretend to be senior executives to trick victims into sharing sensitive information or sending money. Also known as CEO fraud.
C
Clickjacking
An attack where a malicious actor tricks a user into clicking on a malicious link by making it look like something other than what it is.

Cloud computing
The delivery of computing resources (virtual storage, servers, software, etc.) over the internet as an on-demand service.
Cobalt Strike
A penetration testing (“pentest”) tool for Windows systems that simulates how adversaries can attack. Cybercriminals also use Cobalt Strike to carry out attacks.
Learn more: How to Stop Ransomware: See Breach Prevention In Action vs. the Cobalt Strike Backdoor
Common Vulnerabilities and Exposures (CVEs)
Security vulnerabilities and exposures that have been publicly disclosed.
Common vulnerability scoring system (CVSS)
An open framework for evaluating the severity and risk of software vulnerabilities.
Credential stuffing
Automatically injecting lists of compromised login details to other online accounts that may use the same credentials to gain unauthorized access.

Credential theft
A type of cybercrime where threat actors steal login credentials to access secure accounts, systems, and networks, and gather sensitive data and/or escalate access privileges.
Critical infrastructure
Systems, networks, assets, facilities, services, and processes that are vital to the well-being of a country. Damage or destruction to them could have a catastrophic impact on a country’s economy, security, or public health and safety.
Crypter
Software used by attackers to encrypt, obfuscate, and manipulate malicious code to make it look like a harmless program and evade security controls.
Cryptojacking
Surreptitiously hijacking servers or endpoints to mine cryptocurrency.
Cyber incident
An event that threatens the integrity, confidentiality, and/or availability of information systems.
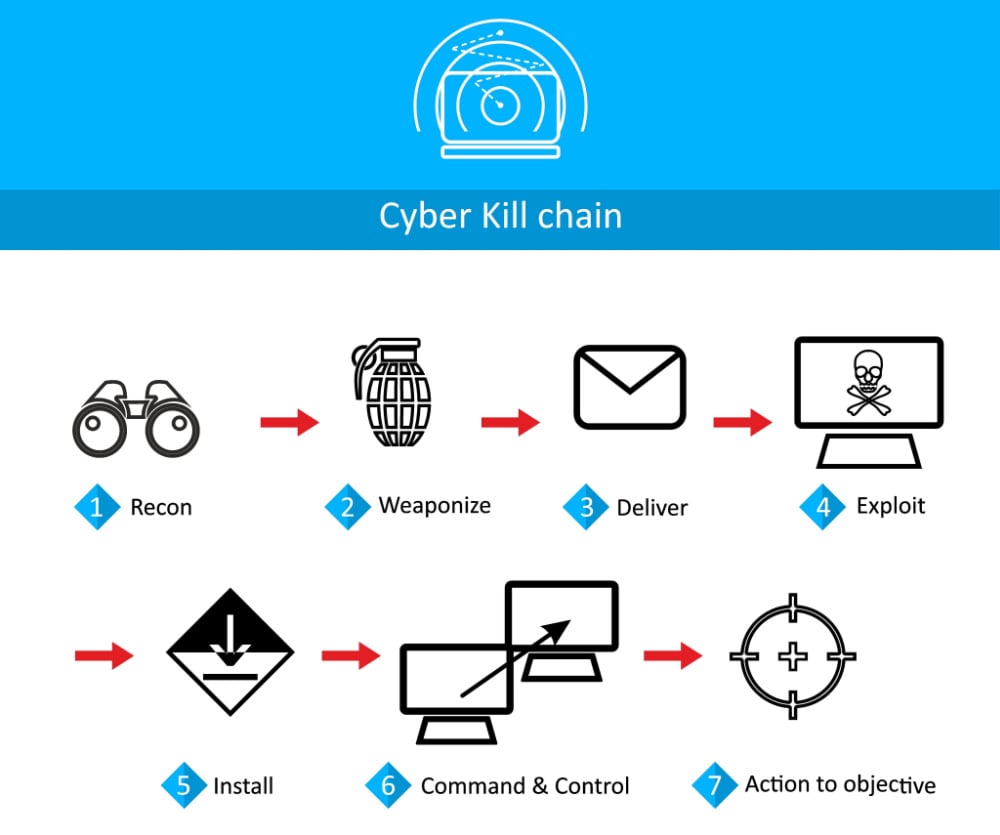
Cyber kill chain
A model that describes the stages of a targeted cyber-attack. Lockheed Martin developed the model by adapting it from the military concept of the “kill chain.” There are seven phases in Lockheed Martin’s kill chain: reconnaissance, weaponization, delivery, exploitation, installation, command & control, and actions on objectives.
Cyber security
The practice of protecting networks, internet-connected devices, and data from attacks or unauthorized access. Cyber security is also sometimes referred to as information technology security.
Cyber warfare
A cyber-attack or series of attacks carried out by one nation-state against another.
D
Dark web
Encrypted web content which isn’t indexed by search engines or accessible through standard web browsers. Users need specialized software to access the dark web, like the Invisible Internet Project (I2P) or Tor browser. These browsers route user web page requests through third-party servers, hiding their IP address.

Data at rest
Data that is in storage. It is not being accessed or used.
Data breach
A cyber incident where sensitive, confidential, or protected data is accessed by an unauthorized party.
Data exfiltration
The unauthorized transfer of data outside a company’s systems by cybercriminals or insiders.
Data in transit
Data that is currently traveling from one system or device to another. Also known as data in motion.
Data in use
Data that is being processed, read, accessed, erased, or updated by a system.
Data leak
The accidental exposure of sensitive data to unauthorized individuals caused by internal errors.
Data loss prevention (DLP)
Technologies and processes that can detect and prevent unauthorized access to critical or sensitive data. Also known as information loss prevention, data leak prevention, and extrusion prevention technologies.
Data mining
The process of analyzing large data sets to find patterns, anomalies, and other valuable information. In cybersecurity, data mining can help an organization identify security threats faster and more accurately.
Decryption
A process that converts encrypted data to its original state.
Defense-in-Depth
A cybersecurity strategy that uses multiple security controls in a layered manner to protect systems from threat actors.
Learn more: Best Practices for Building Defense-in-Depth
Denial-of-Service attack (DoS)
A cyber-attack where threat actors make machines and other network resources unavailable to their intended users. DoS attacks are usually carried out by flooding targeted hosts/networks with illegitimate traffic requests.
Denylist
A list of IP addresses, URLs, domain names, and other elements that are blocked or denied access. Also known as a blacklist or blocklist.
Dictionary attack
A type of brute force attack where cybercriminals attempt to break into a password-protected system by entering familiar words and phrases into the password field using automated tools.

Digital footprint
A unique trail of personal data every internet user leaves behind when engaging in digital activities.
Distributed denial of service (DDoS)
A type of DoS attack that uses many sources of attack traffic. A DoS attack uses a single source of attack traffic. Attackers often use botnets to carry out DDoS attacks.
Domain hijacking
The act of altering or stealing a domain name system (DNS) registration without the original registrant’s permission.
Drive-by-download
The automated and involuntary download of malicious code to a user’s device. Most drive-by-download attacks happen when threat actors inject malicious elements into legitimate websites. A user often doesn’t even need to click or download anything. Their device becomes infected as soon as they visit the site.
Dwell time
The amount of time a threat actor spends in a victim’s environment before being detected.
The E-I of Cyber Security Terms
E
Eavesdropping attack
Unauthorized interception of data in transit between two devices. Also known as network sniffing or network snooping. Eavesdropping attacks happen when a network connection is weak or insecure.
Email hijacking
An email attack where a cybercriminal gains control over a target’s email account.
Encryption
A process that transforms human readable data into an encoded form to stop it from being used/known.
Endpoints
Physical devices that connect to a network, like desktops, laptops, cell phones, and servers.
Endpoint Detection and Response (EDR)
A category of cybersecurity tools that continuously monitor and record endpoint data to detect, investigate, and mitigate malicious activity. When a threat is found, EDR can contain or remove it automatically, or alert security teams.
Learn more: Why EDR Needs Defense-in-Depth to Combat Ransomware
Endpoint protection platform (EPP)
A security solution that uses a mixture of antivirus, data protection, and intrusion prevention technologies to protect endpoints. EPPs are often used in conjunction with EDRs, with EPPs supplying the first line of detection.
Endpoint security
The process of securing endpoints from threats. Also known as endpoint protection.
Evasive threat
Malware that hides its identity to bypass scanning-based security defenses like antivirus software and endpoint detection and response platforms.

Exploit
A piece of code designed to capitalize on vulnerabilities in computer systems or applications for malicious purposes.
Exploit kit
Prepackaged tool kits that automate the exploitation of IT system vulnerabilities. Inexperienced hackers often use exploit kits to distribute malware or perform other malicious actions. Most exploit kits include vulnerabilities that target specific applications, a management console that gives insights into how campaigns are doing, and other add-on functions.
Extended Detection and Response (XDR)
Like an EDR but extends protection beyond just endpoints. Automatically collects and correlates data from different security solutions across endpoints, networks, servers, cloud workloads, and applications. In doing so, XDR breaks down silos, improves visibility, and speeds up threat detection.
F
False positive
A security alert that mistakenly identifies benign activity as anomalous or malicious.
Fast identity online (FIDO)
An open industry association whose goal is to promote authentication standards that reduce people’s and organizations’ reliance on passwords. These include USB security tokens, smart cards, facial recognition, and biometrics.
Fileless malware
Malicious code that hides in process memory rather than installing itself on a hard drive. Since fileless malware leaves no malicious artifacts on the hard drive, it can evade detection by most security solutions. Fileless attacks are also known as non-malware or in-memory attacks.
Learn more: Fileless Malware Will Beat Your EDR

Fingerprinting
An information-gathering process cybercriminals often use to identify targets’ operating systems, software, protocols, and hardware devices. They can then use fingerprinting data as part of their exploit strategy.
Firewall
A network security device that filters all network traffic (incoming and outgoing) to prevent unauthorized access based on predetermined security rules.
Flooding
An attack where threat actors send so much traffic to a system it can’t process genuine connection requests.
G
General Data Protection Regulation (GDPR)
A European Union (EU) law that harmonizes data privacy laws across all member countries. The law gives EU citizens greater control over their personal data and requires businesses to follow strict rules for protecting this data. The GDPR came into effect in 2018. It applies to all companies that operate in the EU or do business with individuals in the EU.
Gray box testing
A security testing technique where testers have partial knowledge of the system being tested.
Gray hat
A gray hat hacker is someone who might violate the law to find vulnerabilities in a system. However, unlike black hat hackers, gray hat hackers usually don’t have malicious intent.
H

Hacker
A person who uses their knowledge of information technology to gain entry in a network or manipulate digital technology in a manner not intended by its original owners or designers.
Honey pot
A decoy system or folder designed to look like a legitimate digital asset. Honey pots mislead cybercriminals away from actual targets. When hackers enter honey pots, security teams can watch their behavior and collect information about their methods.
I
Identity and access management (IAM)
A collection of processes, policies, and technologies that allow IT security professionals to give trusted entities access to the right resources at the right time for the right reasons.
Incident response
The structured approach an organization takes to manage a cyber incident. The goal of incident response is to decrease recovery time, reduce damage and the cost of an incident, as well as prevent similar attacks from happening in the future.
Learn more: Morphisec's Incident Response Services
Indicators of compromise (IoC)
Forensic clues that indicate security professionals a system or network has been compromised.
Infostealer
A type of malicious software designed to steal information from a system, like login credentials.
Learn more: Your Guide to Top Infostealers in 2022
.jpg?width=1000&height=667&name=shutterstock_1092152978%20(1).jpg)
Infrastructure as a service (IaaS)
A cloud computing service organizations can rent to get access to virtualized computing resources.
In-memory attacks
An attack on a system’s memory.
Learn more: Why Should You Care About In-Memory Attacks?
Insider threat
A security risk that comes from individuals within an organization. These include employees, contractors, former employees, business partners, and any other persons with legitimate access to an organization’s assets.
Internet of Things (IoT)
A network of physical objects with embedded sensors that connect to and exchange data over the internet in real time.
Internet of Things security
Technologies and processes for protecting Internet of Things devices and their networks.
Learn more: How Can We Secure the IoT?
Intrusion detection system (IDS)
A security technology that continuously scans inbound and outbound network traffic for potential threats. When an intrusion detection system detects suspicious activities, it alerts IT security teams.
Intrusion prevention system (IPS)
A security technology that watches network traffic for unusual activities and takes preventative action based on established rules. An intrusion detection system can only issue alerts when it spots potential threats. An intrusion prevention system can also block suspicious activities.
The J-P of Cyber Security Terms
J
K
Keylogger
Activity monitoring software that lets hackers record a user’s keystrokes.
L
Lateral movement
A technique used by attackers to move deeper into a victim’s network after gaining initial access.
Least privilege
A security concept in which users and applications receive the minimum levels of access they need to do their jobs.
Legacy system
A computer system, hardware, or related business process that is outdated and not supported by a vendor but is still in use.
Learn more: Can You Secure Legacy Windows Systems?
Linux
An open-source operating system based on the Linux kernel originally created in 1991.
Learn more: Linux Servers: How to Defend the New Cyberattack Frontier
Living off the land (LotL) attacks
A type of attack where threat actors use legitimate functions or software in a target’s IT environment for malicious purposes.
Log4j vulnerability
A critical vulnerability in the popular Apache Log4j 2 Java Library that allows threat actors to remotely take control of a device if it runs specific versions of Log4j. The Log4j vulnerability is also known as Log4Shell or CVE-2021-44228.
Learn more: Protecting Against the Log4j (Log4Shell) Vulnerability
M
Machine learning
A type of artificial intelligence (AI) that makes it possible for machines to imitate human behavior. With machine learning, systems can learn from data and past experiences to predict future outcomes. As the number of data samples increases, so does machine learning’s performance. In cybersecurity, machine learning is used to detect and respond to potential attacks faster.
Macros
A set of commands that automate repetitive tasks in office productivity applications like Microsoft Office. Cybercriminals can abuse macros for malicious purposes. They commonly embed macro malware/macro viruses into word-processing programs or documents, which they distribute via phishing emails. If macros are enabled, malware will execute as soon as a user opens a malicious document.
Malware
Software designed for compromising or damaging information or systems. There are many types of malware, including but not limited to viruses, worms, Trojans, and spyware.

Malware as a service (MaaS)
The illegal lease of malicious software and hardware to customers on a subscription basis. With malware as a service, even individuals without technical skills can launch cyber-attacks.
Malvertising
A cyber-attack technique where threat actors spread malware through online ads.
Man in the middle attack (MITM)
A type of attack where a cybercriminal intercepts and potentially alters communications between two endpoints.
Mean time to detect (MTTD)
The average length of time it takes a security team to discover a security problem within their network environment.
Mean time to respond (MTTR)
The average length of time it takes a security team to contain a security incident after it's identified.
MFA fatigue
A technique used by cybercriminals to bypass multi-factor authentication. MFA fatigue attacks are preceded by brute force attacks. After a threat actor gains a target’s login credentials, they flood the target’s authentication app with push notifications for sign-in approval. Whether the target is inattentive or worn out by the endless barrage of notifications, they often approve the notification.
Mitigation
Minimizing the risk or impact of a potential cyber threat.
MITRE ATT&CK
A knowledge base that classifies and describes cyber-attacks. The term stands for MITRE Adversarial Tactics, Techniques, and Common Knowledge. ATT&CK is community-driven but owned by MITRE corporation, a US non-profit.
Moving Target Defense
Technology that randomizes application memory runtime, obfuscating targets so threat actors can’t find them.
Learn more: Why You Should Care About Moving Target Defense

Multi-factor authentication (MFA)
An authentication method where users must prove their identity using at least two different credential types before receiving access.
N
National Institute of Standards and Technology (NIST)
A non-regulatory government agency that promotes and maintains standards and metrics for technology, science, and other industries in the US.
Learn more: How to Nail Your NIST Cybersecurity Audit
Network
A system of two or more connected devices that can send or share information, applications, and other resources.
Network detection and response (NDR)
A security technology that uses behavioral analytics and machine learning to detect malicious activities on a network. NDRs can respond to potentially malicious activities either via native capabilities or by integrating with other security tools.
Next-Generation Antivirus (NGAV)
A new breed of antivirus software that goes beyond signature-based detection. Most next-generation antivirus solutions include advanced technologies like artificial intelligence, machine learning algorithms, and behavioral detection.
Learn more: 10 Tips To Boost Microsoft Defender AV Security

Next-Generation Firewall
A network security device that combines traditional firewall features such as packet filtering with added capabilities like application control and sandboxing.
NIST Cybersecurity Framework
A set of cybersecurity best practices that organizations can use to manage their security risks. The framework is voluntary guidance.
Learn more: How to Nail Your NIST Cybersecurity Audit
O
Obfuscation
A technique that makes it more difficult to understand code. It can be used to protect intellectual property. However, attackers can also use it to bypass security controls.
Open-source intelligence (OSINT)
The practice of collecting and analyzing freely available data from public sources for intelligence purposes.
Outsider threat
Threats that come from outside the organization.
P
Packet sniffing
A type of software that monitors and intercepts data pieces or data packets traveling across a network.
Patch
Operating system, firmware, application, or driver update that fixes technical issues or known security vulnerabilities.
Patch management
The process of identifying, getting, installing, and managing patches.
Learn more: Your Guide to Virtual Patching
Payment Card Industry Data Security Standard (PCI DSS)
A security standard that sets the minimum data security requirements for all merchants handling, processing, or storing cardholder data.
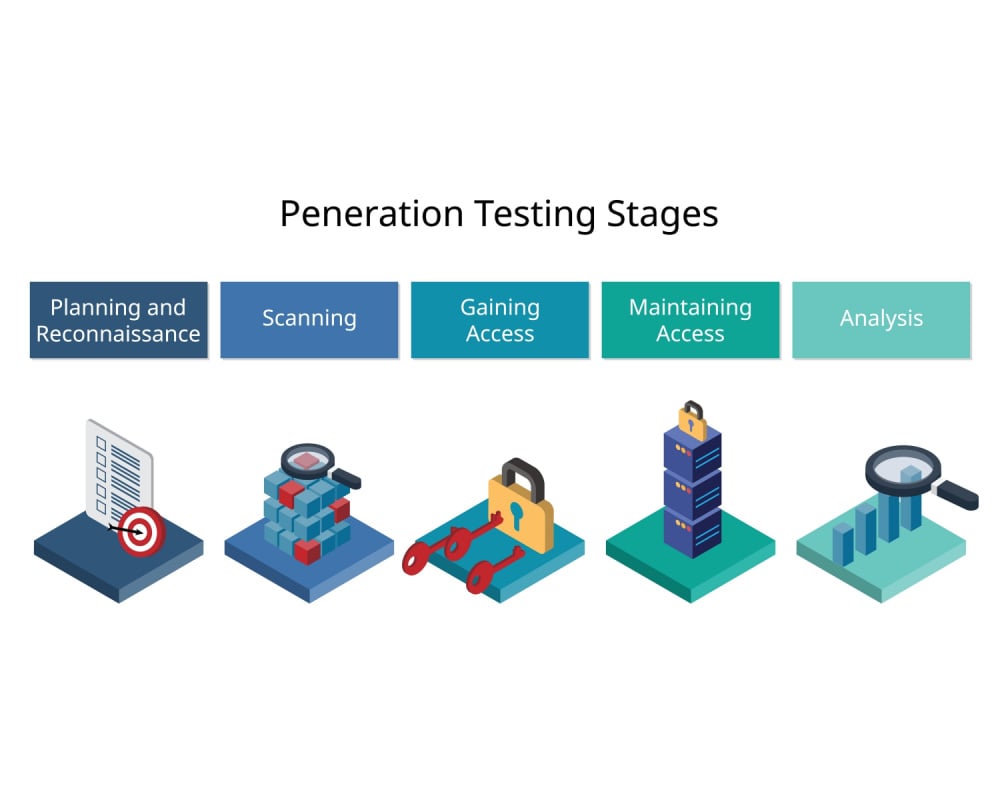
Penetration testing
Known colloquially as pentesting. A simulated cyber-attack against a web application, computer system, or network. The goal of penetration testing is to find any vulnerabilities that could be exploited by threat actors and test defenders’ security posture.
Perimeter security
The practice of protecting an organization’s network boundaries from threat actors. A company’s perimeter acts like a wall between its private intranet and the public internet.
Personally identifiable information (PII)
Information unique to a specific individual that can be used to identify them.
Pharming
A type of attack where threat actors redirect users to a spoofed version of the website they intend to visit.
Phishing
A type of attack where cybercriminals send fraudulent emails or text messages to convince targets to share sensitive information, download malware, or perform some other action.
Polymorphic malware
A type of malware that continuously morphs its identifiable features to evade detection.
Private Health Information (PHI)
Information about a patient’s health condition, whether physical or mental, at any time—present, past, or future.
Learn more: Vital Defense: Ransomware Protection for Healthcare Facilities
Privilege escalation
The exploitation of configuration errors, design flaws, or bugs to escalate permissions and privileges beyond what is usually accessible to a user or application.
Proactive cybersecurity
A cybersecurity strategy that focuses on preventing cyber-attacks from happening in the first place rather than responding to them.
Learn more: What Is Proactive Cyber Defense?
Purple team
A group of security professionals that perform the role of both the red team and the blue team.
The Q-T of Cyber Security Terms
Q
R

Ransomware
A type of malicious software that encrypts a victim’s systems/files or exfiltrates data (or both). To regain access to their systems/files or prevent them from being leaked or sold, companies must pay a ransom to attackers.
Learn more: Staying One Step Ahead: The Ultimate Anti-Ransomware Assurance Checklist
Ransomware as a service (RaaS)
A subscription-based business model where ransomware developers sell or lease ransomware tools to other cybercriminals (“affiliates”).
Reactive cybersecurity
A cybersecurity strategy where attacks are detected and responded to after they happen.
Reconnaissance
The practice of collecting information about a target. Reconnaissance can be passive or active. Passive reconnaissance is gathering data about targets without actively engaging with them. Active reconnaissance is the opposite and involves active engagement with the target, like sending unusual packets to a server.
Red team
A group of security professionals that emulate adversaries to test an organization’s defensive posture.
Remote desktop protocol (RDP)
A network communications protocol that lets users connect to a remote Windows machine.
Remote access trojan (RAT)
A malicious software program that gives threat actors full administrative privileges and remote control over an infected system.
Rootkit
A type of malicious software that gives attackers unauthorized access to and control over a target system. A rootkit is designed to stay hidden in a target system.
S
Sandboxing
A technique used to isolate a program or process from the rest of an organization's system. This can involve running it in an isolated environment, such as an emulator, virtual machine, or container.
Scareware
A tactic used by criminals and malicious vendors to trick users into downloading unnecessary software (such as a fake antivirus), which may itself contain malware.
Scraping
Using a bot or software to extract data from a website. Often done by cybercriminals to find exposed credentials or other data that might enable them to gain network access or conduct phishing scams.
Script kiddie
Relatively inexperienced or unskilled hackers who use off-the-shelf exploit kits and well-known attack techniques to compromise victims.
Security as a service (SaaS)
A cloud-delivered security offering where vendors provide customers with a range of security solutions on a subscription basis.
Security awareness training
Training delivered to non-experts on spotting potential threat actor techniques such as phishing emails and avoiding compromise.
Security information and event management (SIEM)
A type of security solution that collects, analyzes, and reports on data from various sources to detect security incidents. SIEMs collect security logs and alert security teams when certain rules are triggered. E.g., excessive login attempts in a specific timeframe.
Security operations center (SOC)
The group of individuals and systems within an organization that deals with all cybersecurity issues. The SOC is the central point of analysis and action for all security-related data and tools.
Secure web gateway
An application or device which sits between the internet and users within an organization’s network. Used to filter traffic and block malicious content.

Server
A physical or virtual machine that supplies services such as file storage, and/or powers applications.
Learn more: Servers Aren’t As Secure As You Think
Session hijacking
An attack where cybercriminals take control of a user’s computer session by obtaining their session ID and pretend to be the legitimate user on a network’s services.
Shadow IT
The unauthorized deployment and use of IT systems within an organization without the IT department’s approval or knowledge.
Signature
A pattern of behavior associated with a particular malware type or threat actor technique.
SIM swapping
A malicious method of bypassing two factor authentication (2FA) by duplicating or switching the sim card of a victim’s 2FA device with a criminal's one.
Smishing
Using text messages to phish victims or as part of a social engineering attack.
Social engineering
A form of hacking that relies on manipulating human interaction. It is the act of tricking people into performing actions or divulging confidential information.
Spoofing
A technique used to deceive the recipient of an email or other electronic communication into believing a message was sent by someone else.

Spyware
Malware used to watch a victim’s device remotely and steal personal information, credentials, or network information.
SQL injection
A type of web attack that exploits security vulnerabilities in SQL databases linked to online forms. The most common and successful web application hacking technique.
Supply chain attack
A type of cyber-attack where threat actors access an organization's system through a trusted external partner. Also known as a third-party or value-chain attack.
Learn more: How Do You Stop Supply Chain Attacks?
System hardening
Securing a computer system by installing patches, changing default passwords, removing administrator permissions, and other methods of making endpoints and applications as inaccessible to threats as possible.
T
Tactics, techniques, and procedures (TTPs)
Methods used by threat actors to access a system or network.
Tampering
The act of purposely modifying data, systems, system components, or system behavior.
Learn more: Is Your Cyber Security Tamper Proof?
Threat hunting
The process of identifying and mitigating cyber threats. A proactive approach to cybersecurity that involves security analysts using threat intelligence, analytics, and human expertise to identify potential risks before they materialize.
Threat intelligence
Knowledge collected by security teams, vendors, and government agencies about cyber threats and threat actors. Threat intelligence can be collected from various sources, such as open-source data, malware analysis, or human intelligence.
Threat vector
How a threat enters an organization. It can be anything from a malicious email attachment to an infected USB stick.
Triage
How security teams prioritize how to remediate threats and compromised assets within their network.
Trojan horse
Malware disguised as legitimate software or code. It can also be disguised as updates for legitimate software.
Two-factor authentication (2FA)
A security measure that requires users to submit two different ways of proving their identity.
The U-Z of Cyber Security Terms

Unauthorized access
The act of accessing endpoints, networks, data, or applications without permission.
V
Virtual machine
A program or image that lets users interact with a computer system that uses a partitioned element of a separate physical computer’s resources. Virtual machines allow users to run programs as if they were being executed on a physical computer.
Virtual patching
A quick way to mitigate security vulnerabilities and stop them being exploited, to allow fixing the code later.
Learn more: Your Guide to Virtual Patching
Virtual private network (VPN)
A way of encrypting network traffic from a user to a network. Companies often use VPNs to allow employees access to their internal networks from remote locations such as home or while traveling.
Virus
A type of malware that can infect a computer and cause it to do things without the user's knowledge. It can also be used to steal information from a computer.

Vulnerability
A weakness in a system an attacker can exploit. Vulnerabilities can also be found in the design of systems and networks. Vulnerabilities are usually classified as either low or high risk depending on their likelihood of being exploited, and their potential impact if they are exploited.
Vulnerability management
The process of identifying, assessing, and remediating software vulnerabilities within an organization's IT systems.
Vishing
Voice phishing. The practice of manipulating victims over the phone to get them to share sensitive data or perform specific actions.
W
Watering hole attack
A type of attack that implants malware in a website likely to be visited by a victim. This code is then downloaded onto the victim’s computer when they visit the site.
Web application firewall (WAF)
A type of firewall that filters and monitors HTTP traffic to an organization's web application. It can be implemented as a software or hardware appliance, or as a cloud-based service.
Web-based attack
Exploiting vulnerabilities in websites to access databases with sensitive information.
Web server
A type of server that hosts websites and other web services. Web servers store the component types for web pages and other digital assets online and handle HTTP requests from users.

Whaling
A type of phishing attack that targets high-level executives. Whaling attacks typically involve complex and hard-to-spot social engineering efforts that use knowledge about an executive’s professional and personal network against them.
White box testing
A type of penetration testing where testers start with knowledge of their target’s internal structure, logic, and application implementation.
White hat
A hacker who uses their skills to find and fix vulnerabilities in computer systems. Also called ethical hackers.
Worm
A type of malicious software that duplicates itself and spreads across devices in a network.

X
eXclusive OR (XOR)
A binary operation that takes two inputs and returns one output. Commonly used in cryptography to protect against brute-force attacks.
Y
Z
Zero-day attack
A type of cyber-attack that exploits vulnerabilities in software that the software’s developers have not yet discovered. These types of attacks can be extremely dangerous because there are few effective defenses against the unknown.
Zero trust
A security model which assumes any networked device, including the user's own computer, is untrusted. It is a form of the principle of least privilege.
Learn more: The Ultimate Ransomware Strategy: Moving Target Defense + Zero Trust
Moving Target Defense Stops Advanced Cyber-Threats
As the cyber threat landscape gets more dangerous, reducing breach risk becomes accordingly more difficult.
Advanced threats like ransomware, in-memory exploits, and fileless malware attacks are specifically built to bypass current security solutions like AV, NGAV, EPP, EDR, XDR, and SIEM. To stop them, organizations need another security layer, with a different kind of defense technology.
Cited by Gartner as an important emerging technology, Moving Target Defense (MTD) works in-memory at runtime to protect against threats that don’t attack the disc or operating system.
The premise of MTD is simple. Unlike current security solutions, it doesn’t reactively mitigate attacks that target the disc or operating system after they happen. Instead, MTD technology works proactively. It morphs the in-memory runtime environment, making it impossible for threats to find their targets in the first place.
To learn more about how this revolutionary technology works, read the white paper: Zero Trust + Moving Target Defense: The Ultimate Ransomware Strategy.





.png?width=571&height=160&name=iso27001-(2).png)